Almost two years ago, the Specops research team analyzed how long it took to crack passwords hashed with the bcrypt algorithm. Two years is a long time in cybersecurity, so we’re revisiting the research with newer, more powerful hardware,... Read More
Blog
[New whitepaper] How to secure your service desk against social engineering attacks
At first glance, these companies couldn’t be more different. A cleaning products giant, an iconic British retailer, a tech behemoth, and Las Vegas entertainment empire. Different industries, different locations, and different business models entirely. Yet they all share something... Read More
How to optimize Entra MFA with Specops uReset and Secure Service Desk
At Specops Software, we work closely with many customers and assist with the challenges they face in transitioning to more secure authentication methods. This has become increasingly critical as both the complexity and frequency of cyberattacks have increased. Our... Read More
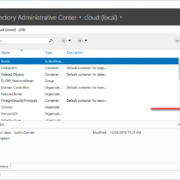
Specops expands cloud offering to self-service password resets
Good news for cloud-first organizations: we’re pleased to announce Specops uReset is now joining Specops Secure Service Desk as being supported for customers who have fully migrated to the Entra ID cloud. Specops uReset is now available for cloud-only... Read More
How to secure hybrid cloud environments: Best practices for cloud password security
As more organizations adopt cloud-first or hybrid IT strategies, identity and access management (IAM) has taken on a new level of complexity. According to a recent report from Flexera, 89% of enterprises now use a multi-cloud strategy, with many... Read More
Stale admin account with ‘123456’ password gives McDonald’s a security scare
Interacting with a chatbot as part of a hiring process feels somewhat dystopian from a candidate’s perspective. In this case, there was almost an added twist when candidate data was nearly exposed thanks to weak cybersecurity controls from the... Read More
Third-party risk: Behind the Google, Chanel, & Air France-KLM breaches
2025 has been a summer of high-profile breaches. This post will focus on four notable and high-profile victims: Chanel, Google, Air France, and KLM. Although the companies and exact data sets differ, these breaches share a clear pattern: attackers... Read More
MFA failure costs Hamilton $18m in cyber insurance payout
On February 25th, 2024, a sophisticated ransomware attack struck the City of Hamilton, crippling roughly 80 percent of its network. This included business licensing, property-tax processing, and transit-planning systems. Cybercriminals proceeded to demand an $18.5 million ransom that the... Read More
How one weak password destroyed KNP: A sad lesson in the cost of password neglect
Businesses fail all the time, for all sorts of reasons. Especially startups and fledgling ventures. So when a business like Knights of Old (trading as KNP Logistics Group) survives a century and a half, through enough recessions, wars, government... Read More
Password spraying: Attack guide and prevention tips
The phrase ‘spray and pray’ likely came from the military, used to describe inaccurately firing automatic weapons in the hope that one shot eventually found its mark. It’s now used to describe any scenario where a strategy relies on... Read More