This website uses cookies to ensure you get the best experience on our website. Learn more
 Datasheets
Datasheets
Specops Device Trust: Zero Trust Workforce Access
Identity alone isn’t enough. If access depends solely on “who you are,” then you’re one session hijacking attack away from...
Specops Password Policy vs Windows Hello for Business
Microsoft Entra ID Password Protection (formerly Azure AD Password Protection) offers a basic layer of security for users, but leaves...
Specops uReset vs. Microsoft Entra ID SSPR
Microsoft Entra ID Password Protection (formerly Azure AD Password Protection) offers a basic layer of security for users, but leaves...
Specops Password Policy vs. Microsoft Entra ID Password Protection
Microsoft Entra ID Password Protection (formerly Azure AD Password Protection) offers a basic layer of security for users, but leaves...
NCSC’s Cyber Assessment Framework (CAF): How to comply with Specops
Specops uReset enables end users to address common tasks related to password management including forgotten passwords, locked out Active Directory...
Specops uReset for Cloud Datasheet
Specops uReset enables end users to address common tasks related to password management including forgotten passwords, locked out Active Directory...
Specops Secure Access Datasheet
Specops Secure Access adds an important MFA layer to Windows logon, RDP and VPN connections, helping organizations better secure hybrid...
First Day Password Datasheet
First Day Password removes the security gap left in many organization onboarding processes: sharing the initial password for a new...
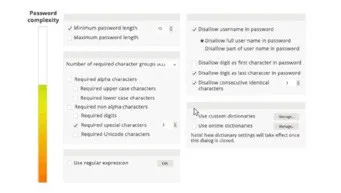
Specops Password Policy Datasheet
Specops Password Policy helps you increase password security in your Microsoft Active Directory environment. You can use Specops Password Policy...
Specops Breached Password Protection Datasheet
Specops Breached Password Protection is a service that continuously checks your Active Directory passwords against a daily updated list of...
Specops Secure Service Desk Datasheet
Employee password resets continue to drive a big volume of the service desk tickets. Aside from draining IT resources, they...
Specops Key Recovery Datasheet
Specops Key Recovery is a self-service solution for unlocking computers encrypted by Microsoft Bitlocker and Symantec Endpoint Encryption. A user...
Specops uReset Datasheet
Specops uReset enables end users to address common tasks related to password management including forgotten passwords, locked out Active Directory...
 Whitepapers
Whitepapers
The Missing Piece in Zero Trust: Device Trust at Every Access Point
Download our free guide that explains how device trust strengthens identity security across the entire session lifecycle.
KuppingerCole Executive View: Specops Software
An independent analyst report on how to improve Active Directory password governance and reduce password-driven risk Passwords still drive breaches,...
How to audit your Active Directory
Download our free guide to detect password-related security risks in your organization.
Securing the service desk
Creating and deploying a new password policy across an entire organization can be a daunting exercise. Once you start, there’s...
Specops Software 2026 Breached Password Report
About the data The data in this report comes from the threat intelligence team at Outpost24, Specops Software’s parent company. In total, over...
How to deploy a Password Policy
Creating and deploying a new password policy across an entire organization can be a daunting exercise. Once you start, there’s...
Specops Password Policy & Breached Password Protection vs. Microsoft Entra Password Protection (formerly Azure AD)
Azure AD Password Protection comes included in P1/P2 Azure AD plans. The name indicates users are protected from using bad...
Microsoft Entra (Azure AD) Self-Service Password Reset competitor comparison
How Microsoft Entra Self-Service Password Reset Works Microsoft Entra (Azure AD) Self-Service Password Reset can be used to change, unlock...
What the Industry is Saying

Great Resource Availability Enhances User Friendliness
The support we received during the configuration and roll out of great, and he was very patient. This product is very customizable to your specific needs and user friendly with great resource availability.

Product Offers Breach Password List and Options
So far, the tool does exactly what the vendor promised, and their support has been helpful when needed and we schedule time with them.

Exploring the Choice Between Passwords or Passphrases
For the moment, thankfully, all worked well ! the policy was simple to set and our brief about the specops tools was clear. I love the feature that allows extending the password validity based on its complexity. It’s great for adding a fun element for users. I also appreciate having the choice between a password or a passphrase and the advanced settings available during software administration.
A great security automation tool for most networks
Our overall experience with Specops uReset has been great and I would recommend it because of the value and service it offers for most networks.




















 Videos
Videos