One of the most critical things that organizations must do in order to ensure the security of their user accounts is to establish a strong password policy, and then ensure that the policy is being enforced. The Windows operating... Read More
Blog
SSPR registration challenges & solutions
As most organizations today are settling into providing remote work solutions to employees, common service desk tasks can become even more challenging for help desk professionals. This can include SSPR registration challenges like password resets, forgotten passwords, locked accounts,... Read More
Security at the Helpdesk
IT departments have always invested heavily in making sure that their systems are able to positively confirm user identities prior to granting users access to sensitive resources. Not surprisingly, there are any number of mechanisms available for authenticating users.... Read More
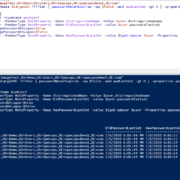
How to find default passwords in Active Directory
What causes identical or default passwords in Active Directory, and how can you find them? A lot of organizations script the creation of new user accounts to standardize, simplify, and speed up the process. Unfortunately, this can also leave... Read More
How to manage Active Directory password requirements
Password policies are a foundational element of any organization’s security posture, especially in environments managed by Active Directory (AD). These policies help ensure that user credentials meet baseline complexity requirements, reducing the risk of unauthorized access. However, understanding and... Read More
The Sectors Experiencing the Most Cyber-Attack Threats While Working from Home, Revealed
Which sectors are experiencing the largest number of cybercrime threats whilst working from home? To do this, we analysed 2,043 different businesses to find out which sectors are most “at risk.” Read More
How to extend Active Directory password expiration times
Balancing security hygiene with user experience is an ever-evolving challenge. While traditional security wisdom has long mandated frequent password rotations, modern authentication frameworks (anchored by MFA, risk-based access, and continuous monitoring) have called those rigid schedules into question. In... Read More
The countries experiencing the most ‘significant’ cyber-attacks
Over the last decade, cyber security has rapidly become a concerning problem. Rightfully so, given how a cyber-attack can compromise an organisation’s key functions and processes within a matter of seconds, exposing sensitive data to opportunistic criminals. The impact... Read More
What’s Your Score? New Executive Summary Reports Available in Specops Password Auditor
Today’s release of Specops Password Auditor makes it easier for you to get sign-off on your password security project. “The IT admins we talk to understand the need for fixing the password vulnerabilities in their Active Directory environments,” said... Read More
How to get decision makers to sign-off on your password security project
While IT administrators often innately understand the cost of not addressing a cybersecurity project, it can be hard to get non-IT management to understand why certain projects should be prioritized. In their July 2018 survey, Spiceworks and AT&T found... Read More