This website uses cookies to ensure you get the best experience on our website. Learn more
ICO’s take on password security
Table of Contents
The UK has officially entered the Brexit transition period until the end of 2020, during which the GDPR will continue to apply. There are three possible outcomes after the transition period: the UK exits transition with no EU trade deal, UK-EU trade deal comes into force, or transitional period gets extended until negotiations are done. For now the default position is no-deal Brexit, in which case GDPR will be brought into UK law as the “UK GDPR” and work in tandem with the UK’s existing Data Protection Act 2018.
If you are a UK business that already complies with the GDPR, and have no contacts in the European Economic Area (EEA) who send you data, and no customers in the EEA, you do not need to do much to prepare for data protection after Brexit; if you’re a UK business or organisation that receives data from contacts in the EEA, you need to comply with GDPR and take these extra steps; if you are a UK business with a European presence or European customers, you will need to comply with both UK and EU data protection regulations after Brexit.
The Information Commissioner’s Office (ICO), the organisation that helps businesses meet GDPR requirements, has provided guidance on data protection after Brexit, click here to view resources.
GDPR still matters regardless of the outcome of Brexit
In practice there will be little change to the core data protection rules from the existing GDPR. Therefore, organisations should still incorporate ICO’s advise on password security into their data protection practices.
Under GDPR, organisations are required to process personal data “in a manner that ensures appropriate security of personal data including protection against unauthorised or unlawful processing and against accidental loss, destruction or damage, using appropriate technical or organisational measures.” Although GDPR does not have any specifications around passwords, they remain an important safeguard to prevent unauthorized access to sensitive data.
ICO password recommendations
According to ICO’s guidance on passwords, a good password system should make it difficult for attackers to access stored passwords in a useable form and should protect against brute force or guessing attacks. It also needs to achieve this without placing an additional burden on users. Complex password rules are ineffective in defending against various password attacks and can drive users to make bad password decisions. The following are the ICO password policy recommendations:
- Password length: Minimum length should be 10 characters and there should be no maximum.
- Password complexity: Don’t mandate the use of special characters.
- Password deny list: Block the use of common and weak passwords. Screen passwords against a password list of the most commonly used passwords, leaked passwords from breaches and guessable words related to the organisation. Update the leaked password list regularly and explain to users why they their passwords have been rejected.
- Password expiry: Get users to create strong passwords and only set password expirations when there are pressing reasons, such as data a breach.
In addition, these defences are also recommended:
- Limitations should be imposed on login attempts
- Use CAPTCHA, whitelisting IP addresses and time limits or delays after failed authentications
- Implement two-factor or multifactor authentication wherever appropriate
Complying with ICO’s password guidance
Although the ICO’s guidance on passwords is not binding, compliance is strongly recommended. During the transition period, the ICO will continue to act as the lead supervisory authority for businesses in the UK.
If you need help implementing all of the ICO’s password recommendations, using a full-featured password solution is the easiest way to do so. With Specops Password Policy, you can replace complexity by banning weak passwords and allowing passphrases to enforce secure policies without burdening users. Additionally, it includes a Breached Password Protection feature that checks against a continuously updated list of compromised, common and predictable passwords.
FREE password audit tool
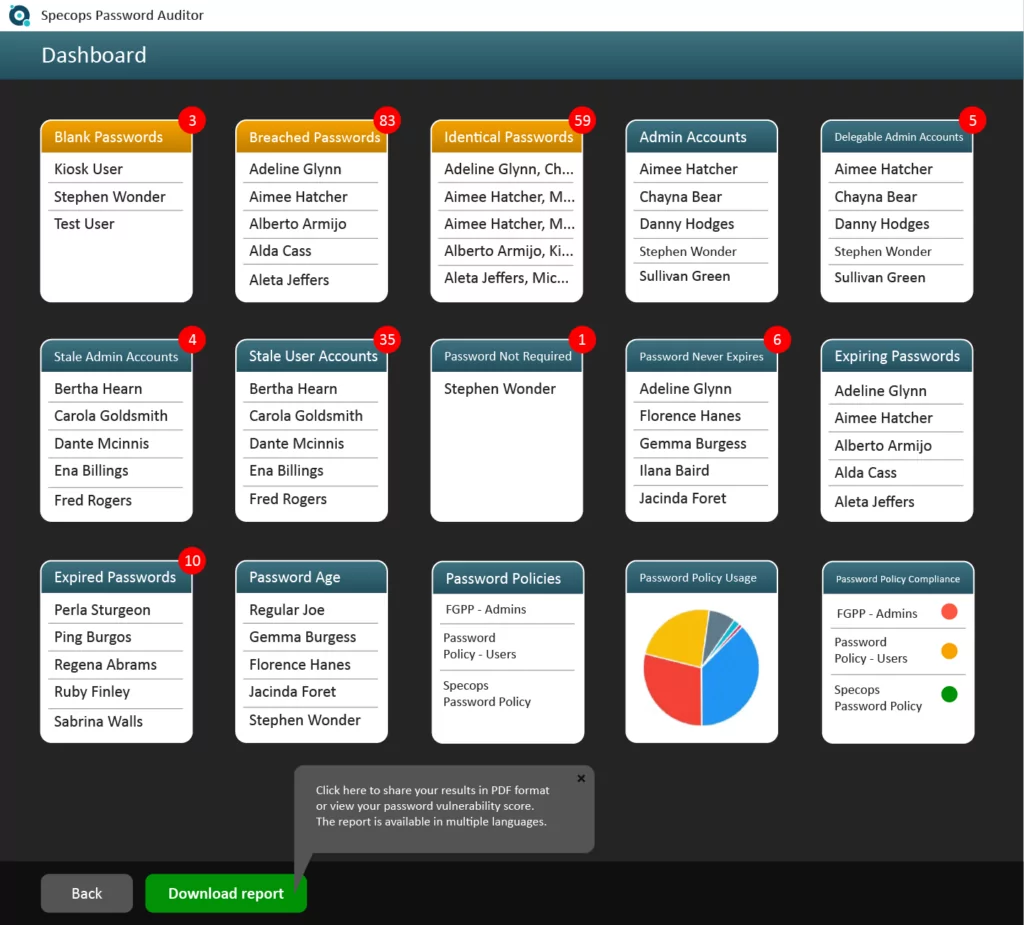
A free tool you can use to find accounts using compromised passwords is Specops Password Auditor. Specops Password Auditor scans Active Directory and checks against a password list of 700 million known-breached passwords. With a quick scan, you can know unlock these key insights:
- Accounts using known-breached passwords
- Accounts using identical or blank passwords
- Accounts with expired or soon-to-be expired passwords
Click here to find out what other password vulnerabilities you can find with this tool.
Contact our password security specialists in the UK:
Call us: +44 (0)203 002 1877
(Last updated on April 8, 2025)

