When employees change their domain passwords, they may still run into issues if their devices have stored old credentials. To avoid login failures and security risks, it’s crucial to reset the cached domain passwords on local machines. Whether employees... Read More
News and Research
Password reset best practices for self-service
Security is an essential part of almost everything we do with technology today. We unlock devices, sign in to websites, and routinely find ourselves verifying our identity, whether we’re online for work, or personal time. In a business setting,... Read More
STUDY: Women in tech reveal the biggest challenges they face
Technology is an exciting industry to be in right now as it is constantly growing and evolving. However, it is well known that the tech industry is highly male-dominated and across the years many people have expressed their concern... Read More
Remote password reset: How to reset passwords & update the local cached credentials for remote users
Need to manage password expirations for remote users? Here's how you can reset passwords for remote users, and update their locally cached credentials. Read More
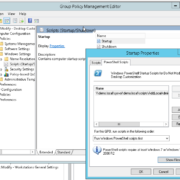
How to configure Specops Password Notification
In this blog post we will review some common configurations for Specops Password Notification. Password Notification is a tool for configuring and sending password expiration reminders to your users. This tool is especially useful for communicating with remote users... Read More
Introducing: Freeware to prevent password expiration during pandemic
Stockholm, April 8, 2020 – Specops Software announced today the release of a free version of Specops Password Notification to help address password challenges associated with remote workers. Password Notification enables IT admins to configure password expiration email reminders... Read More
Evaluating Windows password recovery tools for employee self-service
Nearly every organization, large or small has to deal with the problem of employees occasionally forgetting their passwords. Historically, a forgotten password has meant placing a phone call to the helpdesk. However, this tends to be a very poor... Read More
How to give local admin rights (on a specific machine only) to a domain user
We live in a time where users are working remotely more than ever. This throws IT departments a lot of challenges with regards to support, particularly when it comes to doing it securely. This security challenge has been exacerbated... Read More
How do remote workers connect to your organization’s network?
As COVID-19 drives organizations to remote work, IT admins must suddenly increase the number of remote users they’re supporting. Not only do they need to ensure that these users have what they need to work efficiently, but they also need... Read More
Remote workforce makes organizations more vulnerable to password attacks
With remote working exponentially growing as companies respond to the COVID-19 pandemic, password security has become more important than ever. Specops Software announced today the latest updates to password policy, a solution to continuously check if an account in... Read More