This website uses cookies to ensure you get the best experience on our website. Learn more
 Datasheets
Datasheets
Specops Secure Access Datasheet
Specops Secure Access adds an important MFA layer to Windows logon, RDP and VPN connections, helping organizations better secure hybrid...
First Day Password Datasheet
First Day Password removes the security gap left in many organization onboarding processes: sharing the initial password for a new...
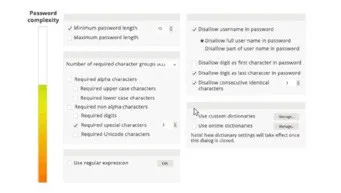
Specops Password Policy Datasheet
Specops Password Policy helps you increase password security in your Microsoft Active Directory environment. You can use Specops Password Policy...
Specops Breached Password Protection Datasheet
Specops Breached Password Protection is a service that continuously checks your Active Directory passwords against a daily updated list of...
Specops Secure Service Desk Datasheet
Employee password resets continue to drive a big volume of the service desk tickets. Aside from draining IT resources, they...
Specops Key Recovery Datasheet
Specops Key Recovery is a self-service solution for unlocking computers encrypted by Microsoft Bitlocker and Symantec Endpoint Encryption. A user...
Specops uReset Datasheet
Specops uReset enables end users to address common tasks related to password management including forgotten passwords, locked out Active Directory...
 Videos
Videos
 Whitepapers
Whitepapers
Specops Software 2025 Breached Password Report
About the data Data in this report comes from KrakenLabs, the Threat Intelligence team at Outpost24 (Specops Software’s parent company)....
How to deploy a Password Policy
Creating and deploying a new password policy across an entire organization can be a daunting exercise. Once you start, there’s...
Microsoft Entra (Azure AD) Password Protection competitor comparison
Azure AD Password Protection comes included in P1/P2 Azure AD plans. The name indicates users are protected from using bad...
Microsoft Entra (Azure AD) Self-Service Password Reset competitor comparison
How Microsoft Entra Self-Service Password Reset Works Microsoft Entra (Azure AD) Self-Service Password Reset can be used to change, unlock...
Case studies
What the industry is saying
Cyber Defense Test Labs: 9.8/10
Cyber Defense Test Labs Team, “In Summary, after 40 years in technology and watching technology grow from mainframes to personal PC’s, handle held phones, with a wide variety of operating systems this is one of the tools that at the start makes a difference in providing a safer environment for the rapid advancing threats from intelligent or state sponsored attacker.”
Gold Award on Privacy PC – #1 in Password management software
Privacy PC, Specops Password Policy is an amazingly flexible toolkit that hardens your organization’s authentication practices to minimize the risk of compromise.

UReset Enables Remote Workforce To Self-Reset Passwords Securely
Network Engineer, “SpecOps uReset deployment process was low-medium complexity but their support team walked us through the entire process and replied to emails within minutes for the most part. The uReset tool works very well but we had several instances of user accounts having attributes that surprised us. This was a result of our own environment lacking some best practices, and uReset helped identify those issues. It works very well from our mobile devices and laptops.”

SpecOps Prevents Bad Password Usage
Director, “Overall this allows us to put in specific blocks for commonly used passwords that we want to avoid in the environment. Microsoft does not give this solution out of the box and has been super helpful.”