This website uses cookies to ensure you get the best experience on our website. Learn more
Analyzing TCP port 21 FTP vulnerabilities
Table of Contents
Port 21 is the gateway through which File Transfer Protocol (FTP) clients and servers communicate. It’s used to send commands and receive responses, making it a critical component of the FTP process. However, this same port is also a common target for hackers due to its inherent security weaknesses. Understanding these vulnerabilities is essential for anyone who uses FTP, whether for personal or professional purposes.
Since the birth of the internet, one of the exciting capabilities it has enabled is the ability to transfer data from one place to another over long distances. One of the first protocols designed for transferring files from one node to another is FTP. However, as cybersecurity concerns and attack risks have escalated, businesses must consider the vulnerabilities associated with port 21 FTP. We’ll explore the port 21 vulnerabilities associated with FTP and the protective measures do companies need to take when transferring files over the internet.
What’s special about port 21?
Port 21 is important because it is the default port used for File Transfer Protocol (FTP) control. FTP is a standard network protocol used to transfer files between a client and a server on a computer network. When you connect to an FTP server, your client typically uses port 21 to establish a control connection, which is used to send commands and receive responses. The actual data transfer, such as uploading or downloading files, usually happens on a different port, often port 20 or a dynamically assigned port. This makes port 21 crucial for initiating and managing FTP sessions.
What is File Transfer Protocol (FTP)?
FTP has been around for quite some time and was designed to transfer files between computers over the internet. FTP works by establishing a connection between two network nodes. It is one of the most frequently used network protocols and, despite the age of the protocol, there are still millions of FTP sites on the internet today.
FTP is a robust and stable protocol often used behind other applications that need to transfer files. Despite being commonly described as port 21 traffic, FTP can also use TCP ports 20 and 21 for a successful connection. Depending on the configuration, FTP may use only port 21 or both 20 and 21. The differences in these connections depend on active vs. passive FTP connections.
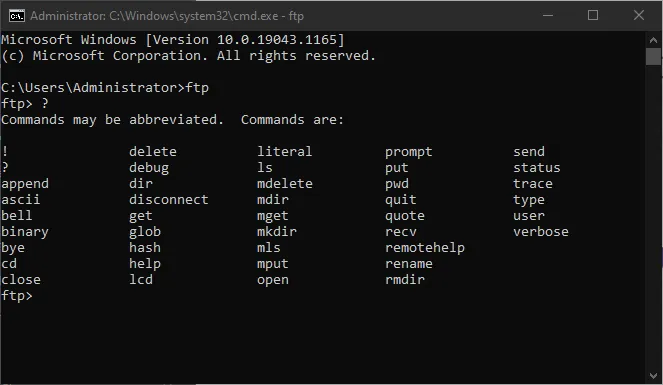
An FTP connection in Windows can be initiated from the command line, using the command ftp. You can see the available command parameters by simply typing a “?” at the ftp prompt. The two most common parameters used with the ftp command are:
- get – download a file from an FTP server
- put – upload a file to an FTP server
Other commercial FTP products provide GUI interfaces and much more robust features than the command line variants built into mainstream operating systems today, such as Linux, macOS, and Windows.
Key vulnerabilities of Port 21
- Plain Text Authentication:
- FTP uses plain text for authentication, meaning that usernames and passwords are transmitted without encryption. This makes it easy for attackers to intercept and steal login credentials using simple packet sniffing tools.
- Anonymous Access:
- Many FTP servers allow anonymous access, which can be a significant security risk. Anonymous users can potentially upload malicious files or access sensitive data if the server is not properly configured.
- Directory Traversal:
- FTP servers can be vulnerable to directory traversal attacks, where an attacker manipulates file paths to access files outside the intended directory. This can lead to the exposure of sensitive files and system configurations.
- Buffer Overflow:
- FTP servers can be susceptible to buffer overflow attacks, where an attacker sends more data than the server can handle, causing it to crash or execute arbitrary code. This can lead to server compromise and data theft.
- Malware Uploads:
- If an FTP server is not properly secured, attackers can upload malware or other harmful files. These files can then be used to launch further attacks or to compromise the server and its connected systems.
- Default Configuration Weaknesses:
- Many FTP servers come with default configurations that are not secure. For example, default usernames and passwords, or unnecessary services running, can provide easy entry points for attackers.
Lack of security
While TCP port 21 FTP is a solid and well-established protocol that has served well for years and still underpins millions of file transfer sites, it lacks in the all-important area of security. Businesses today cannot afford to have lax cybersecurity standards. There is no shortage of attack vectors from ransomware, malware, network snooping, phishing, brute force, and other attacks.
Using legacy and insecure ports and protocols can be a step in the wrong direction for businesses looking to secure their environment and increase their cybersecurity posture. For example, legacy FTP traffic that is transmitted over TCP port 21 is not a secure protocol. Files, credentials, and other information traversing FTP are transmitted in cleartext with no encryption. We often hear about the encryption used by the bad guys concerning ransomware. However, encryption, when used to secure your data, works in favor of security.
It turns easily readable text and string values such as your username and password and turns them into unreadable “jibberish” without the encryption key. With encryption, even if a hacker captures the network traffic, the encryption algorithm makes the data inside the network traffic unreadable.
Businesses need to think about using port 21 FTP to transfer files in their organization due to the unencrypted nature of FTP transmissions. Using FTP can expose sensitive information and network credentials to an attacker when transmitting data across the network or the Internet.
Modern file transmissions should be using more secure protocols such as Secure File Transfer Protocol (SFTP) or SSH over port 22. Both secure file transmission protocols use encrypted communication to secure business-critical data traversing the network.
Another sensitive security vulnerability can be TCP port 3389 – learn more about how to save your Remote Desktop Protocol.
How to protect your FTP server
- Use SFTP or FTPS:
- Switch to Secure File Transfer Protocol (SFTP) or FTP over SSL/TLS (FTPS) to encrypt your data and credentials. These protocols provide a much higher level of security compared to traditional FTP.
- Disable Anonymous Access:
- Ensure that anonymous access is disabled on your FTP server. If you need to provide public access, consider using a more secure method, such as a web-based file sharing service.
- Implement Strong Authentication:
- Use strong, complex passwords and consider implementing two-factor authentication (2FA) to add an extra layer of security.
- Regular Updates and Patches:
- Keep your FTP server software up to date with the latest security patches and updates. This helps to mitigate known vulnerabilities and protect against new threats.
- Firewall and Access Control:
- Use a firewall to restrict access to your FTP server. Only allow connections from trusted IP addresses and implement access control lists (ACLs) to limit user permissions.
- Monitor and Log Activity:
- Regularly monitor and log FTP server activity to detect and respond to suspicious behavior. This can help you identify and mitigate potential security breaches.
The dangers of stolen credentials
Stolen credentials are at the top of the list of dangers to businesses today, both large and small. So why would attackers take the problematic route into your network by trying to compromise a open port vulnerability or other complicated attack if they can easily steal credentials and “walk right in the front door?”
The IBM Cost of a Data Breach Report 2021 noted that a 20% share of breaches is initially caused by compromised credentials making it the most common initial attack vector. Also alarming is according to the same report, on average, a breach caused by stolen credentials took the longest number of days to identify (250) and contain (91) on average for a total of 341 days. So, what is the cost of a data breach caused by compromised credentials? The average cost to businesses from compromised credentials is $4.37 million.
As mentioned, using insecure protocols such as FTP can lead to attackers quickly stealing credentials that are transmitted in cleartext, leading to long, drawn-out, and costly consequences.
Secure your Active Directory passwords and bolster password policies
Due to the risk to businesses that stolen credentials bring, organizations must increase the security of end-user passwords and the password policies that define the types of passwords in an environment. Unfortunately, Active Directory Domain Services, which is used in most enterprise environments today, has limited password policy capabilities. As a result, it lacks the capabilities to satisfy current password policy guidance from cybersecurity authorities, such as breached password protection.
Specops Password Policy is a modern password policy solution that bolsters the native capabilities of Active Directory password policies implemented with Group Policy. Specops seamlessly integrates with existing Group Policy objects and allows bolting on the missing capabilities lacking in Active Directory. Its Breached Password Protection feature also continuously scans your Active Directory against the Specops database of over 4 billion unique compromised passwords. Interested to see how Specops Password Policy could fit in with your organization? Get in touch and we’ll set you up with a free trial.
(Last updated on March 17, 2025)