This website uses cookies to ensure you get the best experience on our website. Learn more
Active Directory and domain controller security best practices
Table of Contents
Windows Servers in the environment housing the Active Directory Domain Services (AD DS) role are some of the most sought-after targets for attackers today. It is because Active Directory contains the credential store for all the user and computer accounts used to secure resources across the enterprise.
As a result, admins need to check their domain controllers security with high-level security practices, procedures, and configurations to keep them secure from attackers. Let’s consider the security best practices for securing Active Directory and domain controllers and see how organizations can help reduce their attack surface.
What is a domain controller?
A domain controller, commonly called a DC, is the Windows Server role housing Active Directory Domain Services (AD DS). Active Directory is essentially a database containing users, computers, and other special objects that allow Active Directory to function to provide identity and access permissions in the environment.
Why attackers go after domain controllers
Businesses have used Microsoft Active Directory in the enterprise data center for years to provide identity and access management functionality. Active Directory is included with Windows Server as a role service that is easily installed and can be configured in a few minutes to provision domain services. Historically, it has made sense for organizations to run Active Directory as they generally have Windows licensed in the data center.
Active Directory is the dominant identity and access management solution across businesses worldwide. According to one report, approximately 90% of Fortune 1000 companies use it as their primary authentication and authorization platform.
Most of the traditional Microsoft solutions in the enterprise integrate with Active Directory to pull permissions from the central identity repository provided by Active Directory services. In addition, most Microsoft solutions use Active Directory permissions for built-in roles and services provided in the application. Examples include Microsoft SharePoint Server, Exchange Server, and others.
Attackers who compromise a business-critical network often look for and attack domain controllers on the enterprise network as Active Directory contains the “keys to the kingdom” in the identity information it contains. Organizations use Active Directory Domain Services to provide the enterprise’s identity and access management capabilities.
Identity Federation
Even though Active Directory Domain Services is an on-premises solution, it can be used for cloud identity. How? In a process called federation, businesses can federate the identities contained in their Active Directory environment with cloud services and solutions. Federating identities from Active Directory means that users can use the same user names and passwords to log into both on-premises and cloud resources.
Compromised credentials are difficult to detect
Compromised credentials are increasingly becoming one of the primary ways attackers make their way into a business-critical environment. Stolen credentials provide arguably the easiest path into the network as they allow the use of legitimate credentials to gain unauthorized access. For an attacker, why go through the trouble of painstakingly compromising an obscure vulnerability when they can “walk into the front door” with stolen credentials? It makes the most sense from a time/effort standpoint.
Note the findings in the IBM Cost of a Data Breach 2022 report:
- The most common initial attack vector in 2022 was compromised credentials, responsible for 19% of breaches
- The cost of an attack as a result of compromised credentials topped $4.50 million USD
Compromised credentials can be very difficult to detect as attackers logging in with a legitimate user’s credentials can easily be mistaken as normal login activity. As a result, it leads to long timelines to identify and contain a breach involving compromised credentials.
- Breaches caused by stolen/compromised credentials took the most extended number of days to identify (243) and contain (84) on average, for a total of 327 days
Active Directory and Domain Controller Security Best Practices
Let’s look at the following ways to secure domain controllers against attack. Like most good security practices and protections, it includes a layered approach.
- Restrict RDP access
- Physical and virtual security
- Regular patching
- Restrict Internet access
- Protect against breached and compromised passwords
1. Restrict RDP Access
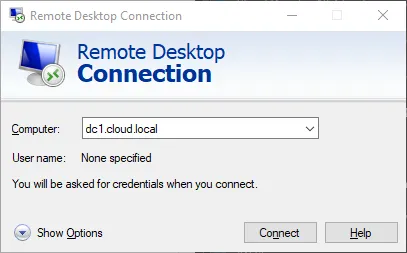
Remote Desktop Protocol (RDP) access provides an easy attack vector for cybercriminals. Attackers can brute force RDP access to find weak or breached passwords in the environment. In addition, unpatched RDP vulnerabilities can lead to ransomware attacks and other types of attacks in the environment.
Ensure to restrict or turn off RDP access for domain controllers in the environment. Using a secure jump host to access domain controllers in the environment is a great way to help reduce the attack surface if you enable RDP on domain controllers.
If you want to take it further, integrate External Attack Surface Management (EASM) to your cybersecurity strategy and monitor your reduced attack surface efficiently.
2. Physical and virtual security
Domain controllers should be treated as sensitive workloads, whether these are run on physical hosts or as virtual machines in a virtualized environment. Therefore, it is a good idea to separate domain controller hosts and VMs from other hosts and VMs in the environment. This separation layer helps to protect against an attacker pivoting from another compromised host or VM in the environment to domain controllers.
If DCs are located in remote or branch office locations with poor physical security, consider using a Read-only Domain Controller that provides a read-only copy of Active Directory and other benefits. Also, encrypting the drives of DCs in the environment offers encryption at rest protection against attack.
3. Regular patching
Domain controllers run on top of Windows Server. It means they need to be patched regularly like any other Windows Server running in the environment. Failing to patch DCs increases the attack surface as patched vulnerabilities can be compromised at a later time by attackers.
According to a recent post, one in three IT professionals, 34%, in Europe admitted that their organization had been breached due to an unpatched vulnerability. It underscores the real-world impact of unpatched systems in the data center. Unpatched domain controllers and other unpatched servers in the environment are dangerous as they provide an attack point for criminals. Long story short, regularly patch your DCs and other servers in the environment.
4. Restrict Internet access
Having Internet access on domain controllers is never a good idea. Often DCs are given Internet access for convenience. However, this is a massive security vulnerability. First, browsing the Internet on a domain controller is never good. Having Internet available lends to this practice and makes it more likely it will happen.
It also allows attackers to run malicious scripts or other code on compromised websites. Browsing the Internet from a domain controller, an attacker has an easy path to compromising the entire environment by stealing credentials and even privilege escalation attacks.
5. Protect against breached and compromised passwords
As mentioned earlier, breached or otherwise compromised credentials provide an easy path to an attacker’s network. Using brute force, credential stuffing, breached password lists, and other types of password attacks, hackers can often easily find breached or compromised passwords used in Active Directory.
Since Active Directory has no native breached password protection, businesses must use third-party tools to add this layer of protection. With breached password protection in Active Directory, it helps to give visibility to and protection against breached passwords used in the environment by an end-user or even an administrator.
Domain Controller protection in AD using Specops Software
Specops provides a wide range of solutions that help increase organizations’ cybersecurity posture today and protect them from password risks. However, good domain controller security hygiene is still critically important, as noted by Specops:
“We also advise our customers to keep domain controller security top of mind as part of the best practice of rolling out our products with domain controller components like Specops Password Policy, whose Sentinel component runs password checks, or Specops uReset whose Gatekeeper component is used to read AD info as part of the authentication process before allowing a password reset.”
Specops Password Policy
Specops Password Policy helps enforce compliance requirements, block compromised passwords, and help users create stronger passwords in Active Directory with dynamic, informative client feedback. Specops Password Policy extends the functionality of Group Policy, and simplifies the management of fine-grained password policies. The solution can target any GPO level, group, user, or computer with dictionary and passphrase settings.
Last updated on November 12, 2025