This website uses cookies to ensure you get the best experience on our website. Learn more
How to remove insecure TLS protocols on your Password Reset System
Table of Contents
A customer recently reported a problem with their Specops DMZ server after users were unable to reset their passwords via the password reset mobile app. The customer reinstalled the DMZ server, but still no success.
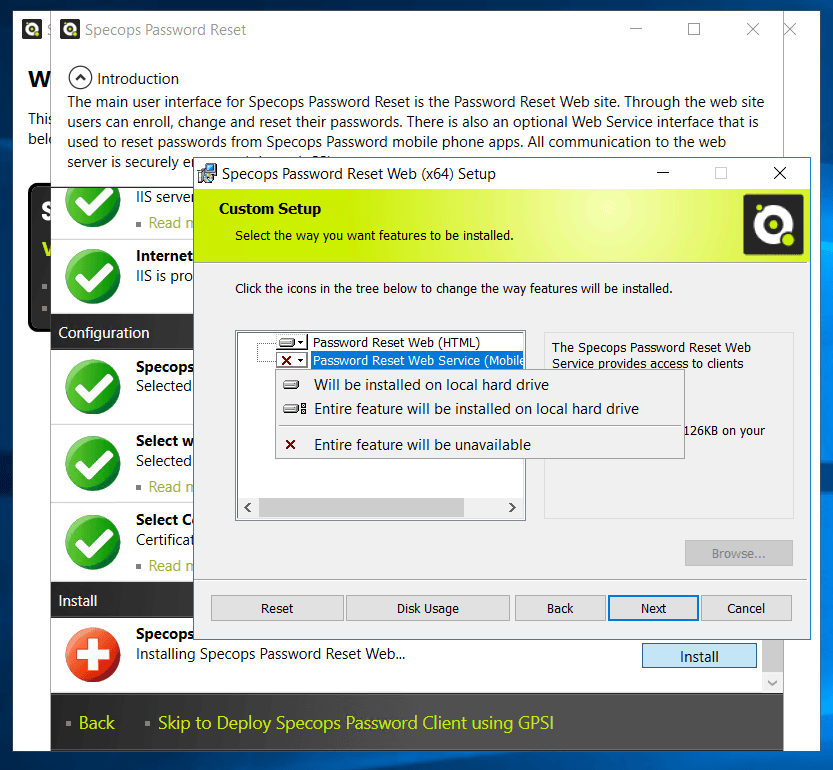
Typically when we run into these problems, we check if the mobile service is installed on the IIS. This can be done by opening IIS and expanding the Specops Password section, checking to see if the “Service” folder is there. If it’s not there, the mobile service is not installed, and you will need to run the Setup assistance on the server, and install the mobile service during the Web setup.
How to remove insecure TLS protocols?
In this case, the service was already installed, and the app was returning “the socket is not connected” error message. After doing some digging, we were able to get the customer up and running with the following:
- Installing .NET 4.6.2 or later on both machines.
- Upgrading to Specops Password Reset 6.6 and above.
- Using the IISCrypto tool to make sure that TLS 1.0 was disabled on both boxes (if we ticked TLS 1.0 it all started to work again, but as that is insecure, we switched it off).
- Enabling Use FIPS compliant algorithms for encryption, hashing, and signing. To do this we used Local Group Policy Editor on both machines and set the setting to enable.
- Rebooting the server so the settings take effect.
- If using the Specops password reset app on Android devices, upgrading the App to the latest version (7.11.17237.2).
This is a solution on how you can remove insecure TLS protocols from your password reset system – if you have any issues please feel free to reach out to our support.
Last updated on October 8, 2024