This website uses cookies to ensure you get the best experience on our website. Learn more

Darren James
Darren James is a Senior Product Manager at Specops Software, an Outpost24 company. Darren is a seasoned cybersecurity professional with more than 20 years of experience in the IT industry. He has worked as a consultant across various organizations and sectors, including central and local governments, retail and energy. His areas of specialization include identity and access management, Active Directory, and Azure AD. Darren has been with Specops Software for more than 12 years and brings his expertise to the support and development of world-class password security and authentication solutions.
Articles written by Darren James
-
Apr
01

How do remote workers connect to your organization’s network?
As COVID-19 drives organizations to remote work, IT admins must suddenly increase the number of remote users they’re supporting. Not only do they need to ensure that these users have what they need to work efficiently, but they also need to…
Read More -
Sep
25

What causes BitLocker Recovery Mode and how to resolve it?
Sysadmins often ask us about BitLocker Recovery Mode. A computer enters into this state when the operating system drive is locked due to a failed system integrity validation. To exit Recovery Mode, the user must enter the correct recovery key for…
Read More -
Jul
03
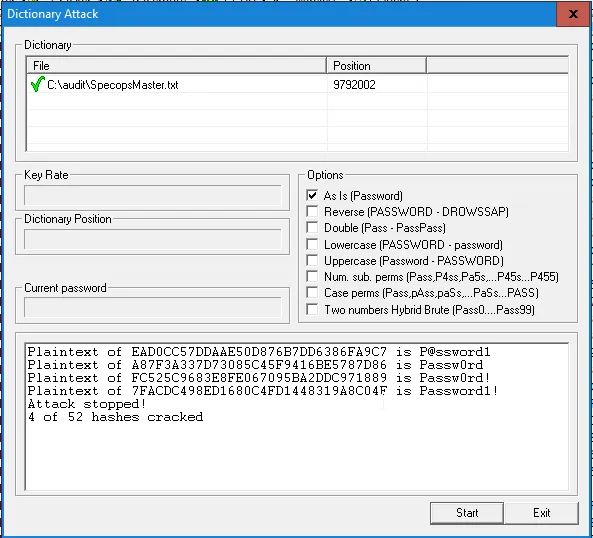
Active directory password audit best practices
Passwords are the bane of any IT Security Officers life, but as they are still the primary way of authenticating users in Active Directory, it’s a good idea to check that your users are making good password choices. Unfortunately, the…
Read More -
Jun
03

How to deploy a MSI package with Group Policy?
Group Policy Software Installation (GPSI) was once hailed as a great incentive for all organizations to upgrade their NT4 domains to Active Directory. It meant that there was no longer a need for those complex application deployment tools, it can…
Read More -
May
22

How to enforce password history in Active Directory
The “Enforce password history” setting in Active Directory is used to determine the number of unique passwords a user must use before they can use an old password again. This is an important setting because password reuse is a common…
Read More -
May
08

What are the benefits of Full Disk Encryption
Full (or Whole) Disk Encryption (FDE) is a phrase used to describe the encryption of a computer hard drive(s) so it is not easily readable by an unauthorized user. As the name suggests, because this is done at disk level…
Read More -
May
02

How to change user passwords in Active Directory
We often get asked how our self-service solution changes passwords on a user account in Active Directory. It’s a more interesting question than it sounds as there are many processes at work here, and many ways to do it. I…
Read More -
Apr
01

Guide to NCSC’s Cyber Essentials password policy compliance
Recognized as the authoritative voice on information security in the UK, the National Cyber Security Centre (NCSC) is the UK’s weapon in securing IT. The NCSC consolidates and replaces existing expertise, and indicates the prioritization of cybersecurity on the national…
Read More -
Mar
18
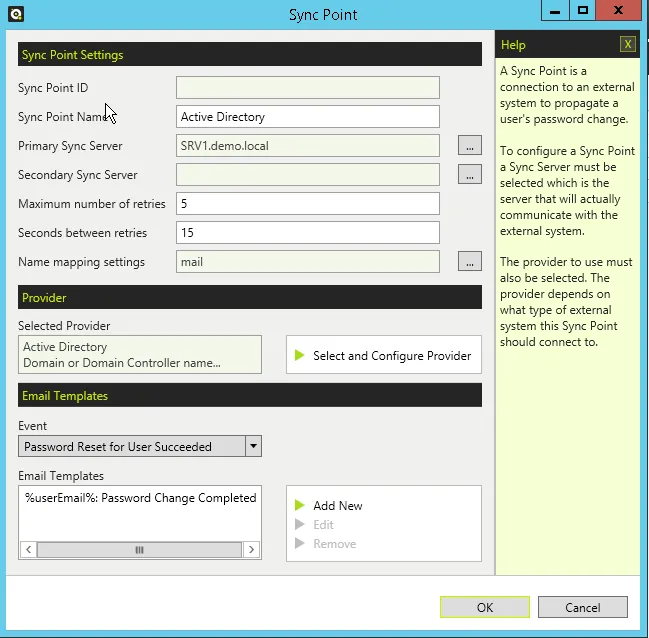
Sync passwords between Active Directory domains
There are many reasons why you might want to sync a password between two Active Directory (AD) domains. We commonly see requests from customers who are looking at migrating their users from one domain to another. This could be for…
Read More -
Oct
23

How and why the NHS should transform password policy for greater security
As the largest employer in the United Kingdom, and the fifth largest in the world, the NHS has a responsibility to lead the way in cyber security. After all, there's much at stake. For a high profile and public-facing organisation…
Read More
