This website uses cookies to ensure you get the best experience on our website. Learn more
How to configure the NCSC password list in AD
Table of Contents
Passwords are one of the weakest links when it comes to ensuring that your environment is secure. Traditional user accounts and the associated passwords have long been the default security mechanism found in most environments. With the very advanced and evolving threats that exist today, passwords are certainly one of the primary targets of cybercriminals.
Attackers realize that users generally choose easy to remember passwords or passwords that are commonly used by many different users. They then focus on these commonly used weak passwords to compromise target environments. The UK’s cyber security authority, the National Cyber Security Centre (NCSC) has produced a list of the top 100,000 passwords originating from the “Have I Been Pwned” data list which helps organizations to have a listing of commonly used weak passwords that have been found in actual data breaches.
How can your organization make use of the NCSC resource? How can you scan for and prevent the use of weak passwords in your environment such as those found in the NCSC password list? Let’s take a look at scanning for and auditing passwords in your environment effectively.
Who is the National Cyber Security Centre (NCSC)?
First of all, who is the National Cyber Security Centre (NCSC)? The NCSC is London-based security organization that protects organizations in the UK from data breach and also provides effective incident response to help minimize the effects of cyberattacks. They also publish the Cyber Essentials which contain guidelines to make passwords compliant.
The NCSC provides practical cybersecurity guidance to both organizations and individuals. They respond to cybersecurity incidents to help reduce the fallout and effects of a cyberattack across a broader attack surface. They work to secure both public and private sector networks.
They provide a single point of contact for SMEs, larger organizations, government agencies, and the general public. They also carry out efforts to work closely with law enforcement officials as well as intelligence and security agencies and international partners.
How can disallowed password lists help?
You may wonder, how can disallowed password lists help to make your environment more secure when it comes to cyberattack? The NCSC has noted, along with other very reputable security organizations, that including disallowed password lists as part of password security mechanisms is a great way to bolster password security.
In conjunction with the NCSC, note what is found in the NIST Special Publication 800-63B – Digital Identity Guidelines:
“When processing requests to establish and change memorized secrets, verifiers SHALL compare the prospective secrets against a list that contains values known to be commonly-used, expected, or compromised. For example, the list MAY include, but is not limited to:
- Passwords obtained from previous breach corpuses.
- Dictionary words.
- Repetitive or sequential characters (e.g. ‘aaaaaa’, ‘1234abcd’).
- Context-specific words, such as the name of the service, the username, and derivatives thereof.
If the chosen secret is found in the list, the CSP or verifier SHALL advise the subscriber that they need to select a different secret, SHALL provide the reason for rejection, and SHALL require the subscriber to choose a different value.”
Another good reason to use these types of lists is that hackers use them. What do we mean? Hackers often use lists of commonly used passwords to do what is called password spraying. Password spraying is where hackers use lists of a small number of common passwords to brute force a large number of end user accounts. Out of hundreds of thousands or millions of accounts, there is a good chance that at least a few users will be using a known password found on the list.
As a defensive measure, using the same types of lists to both find and limit the accounts in your environment that may be using a breached password, helps to give visibility and protect against password spraying in your environment. The point here is that you want to find weak and re-used passwords before an attacker does.
Disallowed password lists help to shed light on an age-old problem that end user’s fall victim to – password re-use and weak passwords. End users generally have an affinity to using “easy to remember” passwords such as “123456”. It could also be easy to remember names, dates, and other common items that are used as part of passwords.
Many organizations may feel they are protected since they use an account lockout mechanism such as found in Active Directory to protect against brute force attempts. The problem with account lockouts is there is generally a threshold of attempts before the account is locked out. Additionally, accounts locked out due to bad password attempts may also reset after a period of time, allowing an attacker to try additional passwords against the account.
A persistent attacker may be able to try hundreds or thousands of common passwords against accounts without any sort of red flag raised in the environment if this is done in an inconspicuous way. This may be carried out over days or weeks of brute force attempts, so as not to raise suspicion.
Using the NCSC “Pwned” Password List
Using the password list from NCSC that contains 100,000 of the top compromised passwords that have actually been exposed in breaches can be done using a PowerShell script provided by NCSC. The script for the NCSC password list is freely available for download here. Using the script, you can feed the PowerShell code any file containing password lists that you want to use to check your environment. So, what I have done is downloaded the “PwnedPasswordsTop100k.txt” file and passed this into the PowerShell script.
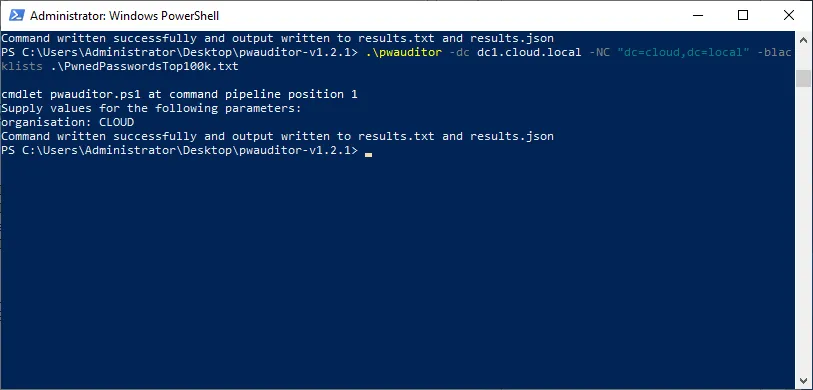
Looking at the results file, you can see the results of checking Active Directory against the Top100k.txt file.
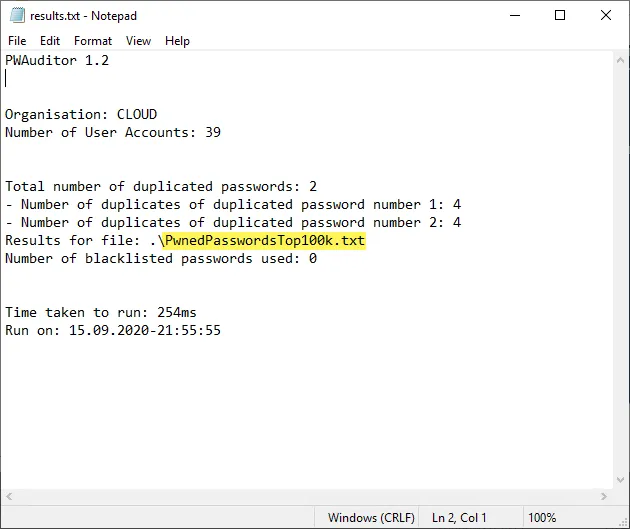
The NCSC PowerShell script is a great little tool that allows easily checking your environment using built-in PowerShell tooling and the quick download of the password file.
Using Automated Disallowed Password List Scanning
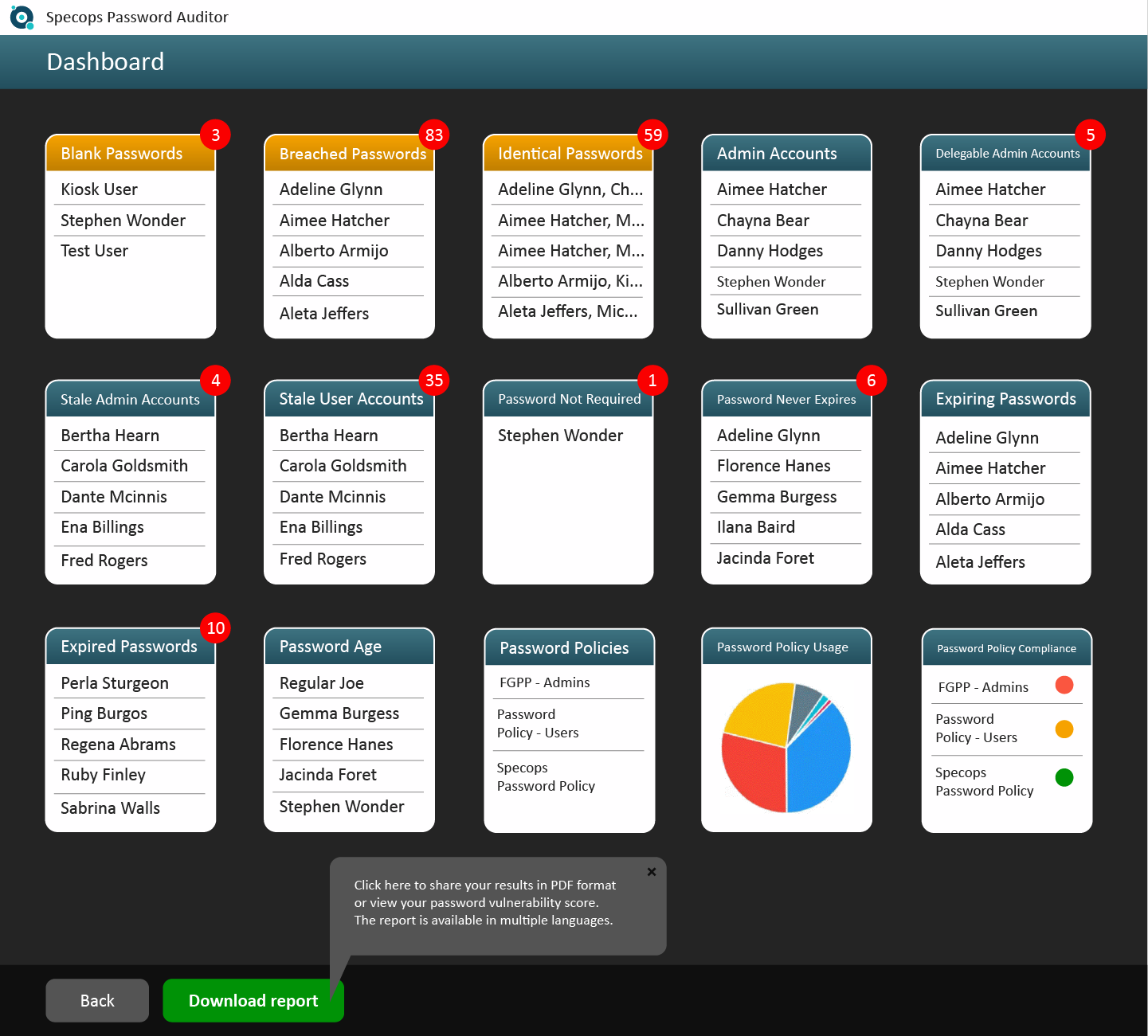
While the PowerShell script produced by the NCSC is a great place to start checking for risky passwords, using more automated and dynamic tooling to check the passwords in your environment is even better. A really powerful tool, freely available to check passwords in your environment, is Specops Password Auditor. This is a free tool that provides access to updated disallowed password lists for scanning your environment that goes beyond functionality offered by the PowerShell script and other tools.
As a case in point, the NCSC Top 100k password list did not flag passwords I had assigned to a handful of test accounts. Specops Password Auditor however did flag these accounts for identical passwords as well as breached passwords. Note the checks in the environment, including:
- Blank passwords
- Breached Passwords
- Identical Passwords
- Admin Accounts
- Stale Admin Accounts
- Password Not Required
- Expiring Passwords
- Expired Passwords
- Password Policies
- Password Policy Usage
- Password Policy Compliance
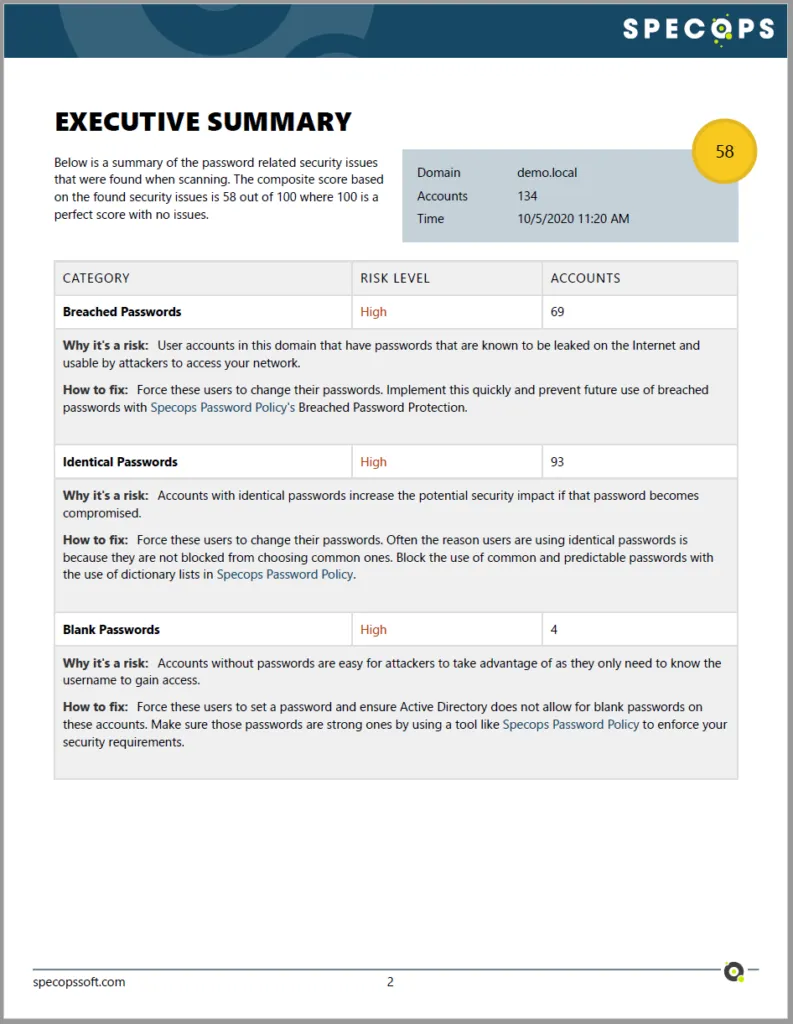
Additionally, Specops allows creating detailed reports that can be sent to management as well as produced for internal audits. Below is an example of a quick report created from the information displayed above. The password risks are broken out between categories and assigned a risk level.
This helps to ensure these are prioritized based on criticality. You also have quick directives given on how to fix the associated risks.
Specops also has another tool called Specops Password Policy which offers a Breached Password Protection Service to continuously block the use of 4 billion compromised passwords in your Active Directory environment. The service checks for passwords found in leaked data, malware botnets, and an extensive honeypot system that monitors for passwords being used in brute force attacks happening right now. This provides the automated tooling needed to help enforce good password hygiene in your environment.
Automated solution to stop the use of breached passwords
Weak and re-used passwords introduce tremendous risk in your environment. Attackers often use passwords that have been found in previous breaches as these are commonly used across many different environments. If attackers use password lists, it is a good idea for organizations to use their own password lists containing breached passwords to both identity and prevent their use among end users.
The NCSC has produced a list of passwords that comprise the top 100,000 passwords that are used across many environments and that have been found in previous password breaches. Using this list along with PowerShell, you can scan your environment to identify user accounts using the breached passwords.
Using automated tools like Specops Password Auditor and Specops Password Policy allows you to find weak, reused, and breached passwords that are already in use, and prevents users from selecting compromised passwords in the future. This helps to prevent cyberattacks that target vulnerable passwords in use in the environment.
Check out Specops Password Policy and how it can help create compliant password policies, and target password entropy here.
(Last updated on April 8, 2025)



