This website uses cookies to ensure you get the best experience on our website. Learn more
Keep MFA running during identity service disruptions
Table of Contents
Specops Authentication is the MFA platform that secures password resets, and encryption key recoveries via self-service, and/or at the IT service desk. One of the unique features in the Specops Authentication platform is the flexible MFA. This feature keeps the aforementioned use-cases operational, even if a primary identity service is unavailable.
In this article, we’ll talk through the scenarios that might cause identity service disruptions, and best practices to keep MFA running in Specops Authentication.
What can cause MFA disruptions
- User device is lost or stolen: Some identity services (for example, one-time passwords in Google Authenticator) may be permanently gone if the user loses access to their device. You may have seen recent news about Google Authenticator attempting to solve this issue with a new syncing feature, however there are some important security considerations to keep in mind before enabling this feature for employees.
- Identity service is down: Identity service disruptions are not uncommon. While these are mainly temporary, they can be extremely disruptive to the service desk, and productivity.
- Identity service is compromised: If an external identity service is suspected of compromise, you may want to disable it altogether, while having alternative options to securely authenticate users.
How to configure your MFA policy to minimize disruptions
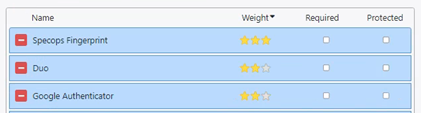
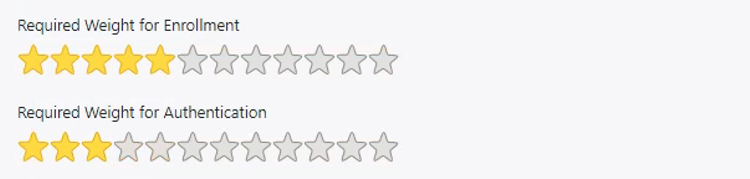
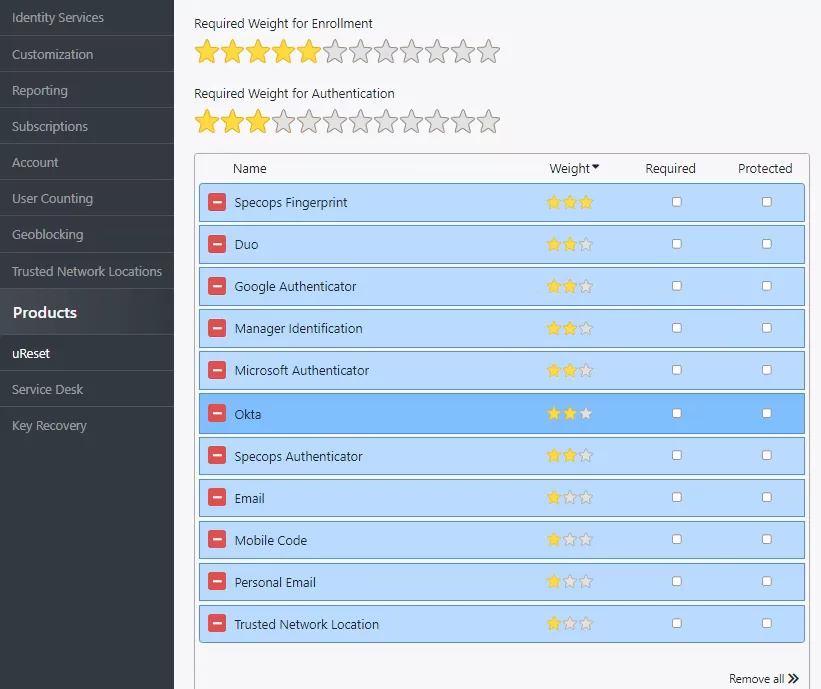
When configuring your Specops MFA policy, consider a layered strategy to keep MFA always available. The MFA policy is based on the number, and types of identity services available to users, as well as their security (star) assignment. The system allows you to assign a higher value (stars) to those identity services you believe provide a higher level of security.
Consider the following when creating your MFA policy:
- Enabled identity services: The enabled identity services are available to users during enrollment. With more identity services to choose from, users have the flexibility they need to successfully enroll and authenticate.
- Identity service enrollment requirements: The enrollment policy determines the number and types of identity services required for enrollment. To provide users with flexibility, ensure that the enabled (available) identity services exceed the enrollment requirements.
- Identity service authentication requirements: The authentication policy determines the number and types of identity services required for a successful authentication. To provide users with flexibility, ensure that the enrolled identity services exceed the authentication requirements.
What identity services to enable
For a full list of the available identity services in the Specops Authentication system, click here. For best practice, we recommend enabling at least 2 identity services from the Standard category, and at least 1 identity service from the 3rd Party category. There is also the option of adding identity services from the Federated category, which would provide additional “non-mobile” based authentication if appropriate.
Identity service weight (star) assignment
As previously mentioned, Specops Authentication allows you to assign a specific weight (stars) to each identity service. The weight assignment should be aligned with the deemed security of the identity service. The most secure identity service can be assigned with most stars. This means that if it is chosen during authentication, the system may not require additional verification with other factors.
To help you select the best identity services for your organization, we have created the below matrix, featuring the most popular identity services, and the following consideration criteria:
- The MFA factor the identity service addresses: something you know, something you are, something you have
- The enrollment flexibility: pre-enrollment and/or administrator enrollment using existing Active Directory data
- Mobile device dependency
- Resistance against MFA fatigue attacks
| Identity Service | Something you know | Something you have | Something you are | Pre/Admin enrollment | Mobile phone based | Active Directory data | MFA fatigue resistant |
| Duo Security | x | x | x | x | x | ||
| Manager Identification | x | x | x | ||||
| Specops Fingerprint | x | x | x | x | |||
| Symantec VIP | x | x | x | x | x | ||
| Trusted Network Locations | x | x | |||||
| TOTP Google and Specops Authentication or | x | x | x | x | |||
| TOTP Microsoft | x | x | *Depends on user configuration | x | *Depends on user configuration | ||
| Yubikey | x | x | x |
What to do in the event of a disruption
If you are currently experience an identity service disruption, here’s what you should do:
Your MFA policy supports additional identity services
- Communicate with end-users: Inform them of the disruption, and outline any actions that need to be taken on their side.
- If it’s going to be a long-term disruption, and depending on what your enrollment and authentication policy looks like, you can either:
- Disable the identity service altogether.
- If it’s not as trustworthy as it once was, reduce the number of stars for the affected identity services.
Please note the following:
- These actions may trigger enrollment enforcement again as the user’s current number of stars for enrollment may now drop below the required amount.
- You can force users to re-enroll on an individual basis using the Service Desk web portal, or you can use a PowerShell script to force re-enrollment globally.
How to add/edit/disable an identity service
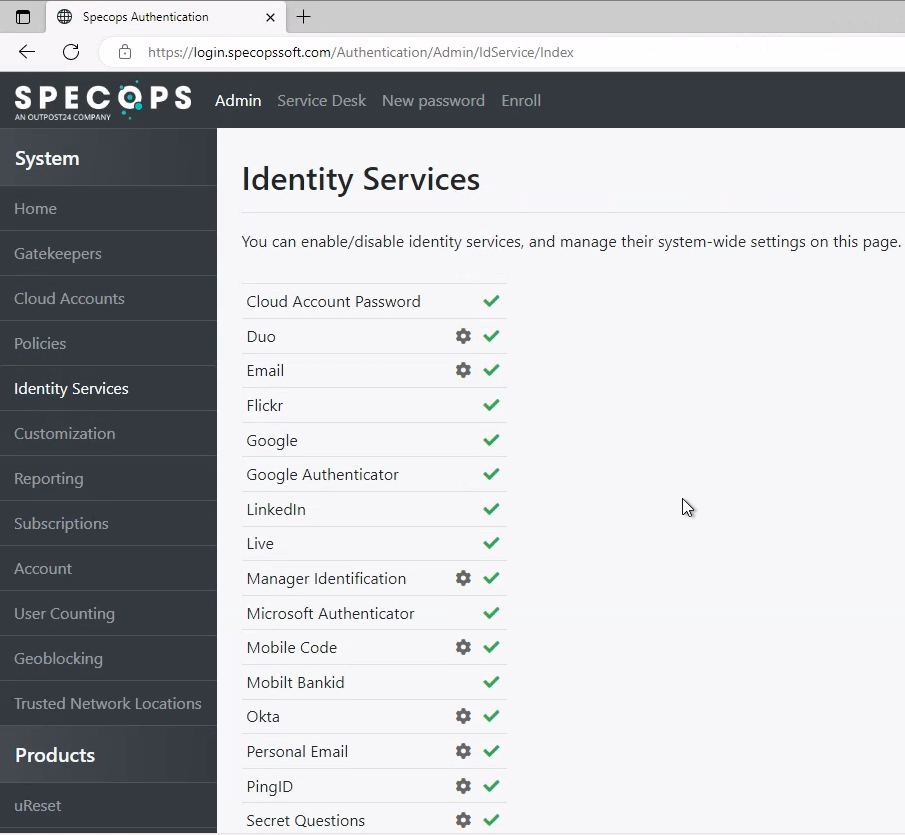
On the Specops Authentication Web, you can find a full list of available identity services under the Identity Services tab. You can enable/disable all of the identity services in this list. You can also configure some of these identity services and manage their system-wide settings on this page.
Support from Specops
For more questions or additional support on how to best configure Specops Authentication up for your organization, contact Specops (Outpost24) Support.
Last updated on September 29, 2025