This website uses cookies to ensure you get the best experience on our website. Learn more
Custom ADMX templates for the Specops Authentication Client with Specops Password Reset
Table of Contents
One of the great things about Specops Software solutions is that they are designed to require as little installation effort as possible. This means that our customers can get a system up and running very quickly, usually zero impact on any other system.
Of course, sometimes we might need to customize the behavior of our solutions. When it comes to the client-side software, we need to do this across a large number of machines. This is where we use of ADMX templates, which allows administrators to tweak the behavior of that client.
The client and the ADMX templates support all of our authentication products, so you may see it referred to as the Specops/SPR/uReset/SPP Client – however, its unified name is officially the Specops Authentication Client.
This article will cover the Authentication Client and the ADMX templates used with our Specops Password Reset (SPR) solution.
Where do I get the ADMX templates?
You can find them on the download page in the SPR support page:
https://specopssoft.com/support/password-reset/download
Once the templates are downloaded and extracted locally, we recommend that you copy them to the ADMX Central Store on your AD’s SYSVOL share. This will make them available from any admins Group Policy Management Console. You would copy the files to the following locations:
Specops.Authentication.Client.admx would be copied to \\[domain]\SYSVOL\[domain]\Policies\PolicyDefinitions
Specops.Authentication.Client.adml would be copied to \\[domain]\SYSVOL\[domain]\Policies\PolicyDefinitions\en-US
What Customizations can I make?
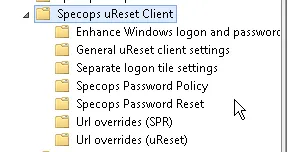
If you open Group Policy Editor, and look under Computer Configuration>Policies>Administrative Templates>Specops uReset Client you will see the following: uReset Client
As mentioned in the introduction, you will notice that all Specops solutions that the client works with are represented here. Some settings will work across the product range while others are more specific. With Specops Password Reset in mind, let us look at each folder in turn.
Enhance Windows Logon and Password Change
Show Reset Password Link even if the connection to Active Directory can’t be verified – If you want Specops Password Reset to be available to users when they take their business laptops/tablets outside of the network, this is a good option to enable. This setting forces the display of the “Reset Password…” link on the ctrl-alt-del and lock screen pages. This should be used in conjunction with the URL Overrides setting that specifies the external URL of the Reset page.
Enhance Windows logon and Password Change interface – For SPR, this setting simply enables/disables the “Reset Password…” link. This can be useful if you want to deploy the Authentication Client in advance of installing the server components.
GUID of credential provider to wrap – Part of the Specops Authentication Client is a Credential Provider that wraps the default Microsoft Credential provider (the login screen), and allows us to place the “Reset Password…” link on the ctrl-alt-del/lock screen.
Sometimes there might be other third-party clients, such as endpoint encryption software, that also wrap the Microsoft CP and stop the “Reset Password…” link from appearing. If this is the case, we want to avoid any potential conflicts. This setting will allow you to wrap the third-party CP instead of the MS CP.
To do this, you will need to find the GUID of the third-party CP and place that GUID, along with the curly brackets, into this GPO setting. You can find this GUID in the registry of the client OS:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\Credential ProvidersCurrentVersion\Authentication\Credential Providers
There will be a lot of GUID keys and one of them will be the offending 3rd party CP. Each one should have a description in it so it normally is not too difficult to find, but if you are having issues, contact Specops Support and we should be able to point you in the right direction.
A final note on this – not all third-party CP’s support wrapping so this should be tested in each case before deployment.
General uReset Client Settings
Ask user if certificate has warnings – As SPR is a security product, we do our utmost to make sure that it is protected from compromise. Our software takes advantage of PKI Certificates, and if any of the following is detected, the securedbrowser part of the client will stop in its tracks:
- The certificate is not issued by a trusted CA
- The certificate chain is broken by HTTPS inspection
- The name of the URL doesn’t match the webpage
- The certificate has expired
- The certificate revocation list servers cannot be reached
If this setting is enabled, it will allow the securedbrowser to continue, but only after confirming with the user that it is OK to do so.
Create start menu shortcuts to password enrol/change/reset – This option can be used to remove the start menu shortcuts for enroll, change, and reset.
Enable local registry caching of the ExternalURL from SCP – All the URL’s for the different webpages that the client connects to are stored in something called a Service Connection Point (SCP) – a subobject on the Server Object in AD. This setting tells the client to cache the ExternalURL value for use when the client needs to operate externally. Normally this does not need to be set as this particular scenario can be achieved using other methods e.g. enabling the “always show password reset link” and adding the externalURL value into the URL Overrides section.
Prefer SPR over uReset – By default, if the client detects that SPR and uReset are installed in the same domain it will try to connect to the uReset tenant first. If you need the opposite, in scenarios where you are migrating from SPR to uReset, you may wish to override this behavior.
Interval between checking AD for notifications – Specops Password Reset has several enrollment enforcement options. One of those options prompts the user to enroll by displaying a balloon tip at logon, and then every two hours after they login until the enrollment is complete. This option allows you to alter that 2-hour interval.
List of languages for which start menu shortcuts are created – By default, the client will create the shortcuts using the language of the local SYSTEM account. However, if you wish to override that behavior, you can configure the language here. You must use IETF tags e.g. en for English, and sv for Swedish, etc. Multiple shortcuts in multiple languages are also supported, just separate the tags with a comma e.g. en,sv,de.
Separate Logon tile settings
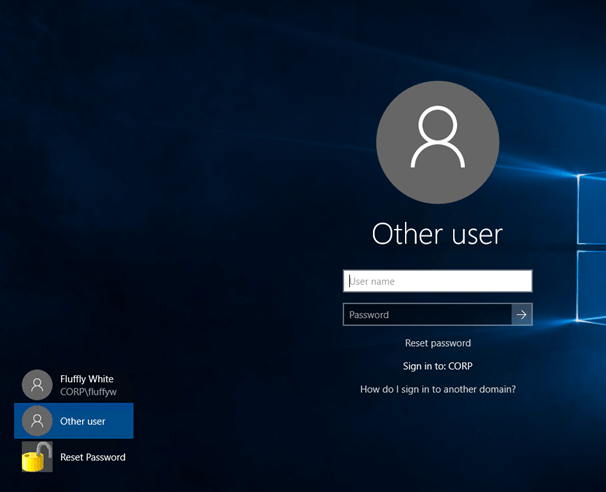
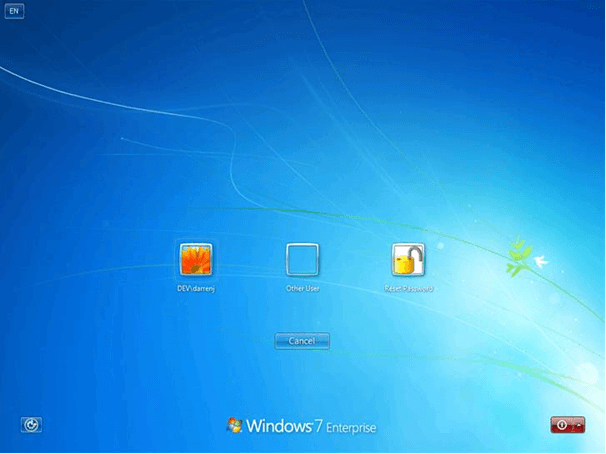
Enable Separate Password Reset Logon Tile – We discussed about the ability to wrap a third party credential provider, with a note that not all third-party CP’s can be wrapped. If this is the case, you can use a logon tile instead to enable your users to access the Reset password page from the ctrl-alt-del/lock screen.
On Windows 10/8.1./8 it appears like this: 8 it appears like this:
And on Windows 7 like this:
Custom bitmap path – if you do not like the Yellow padlock you can define a custom 128×128 pixel bitmap to be used instead.
Specops Password Reset Password Reset
Name of attribute used for Mobile number (to override ‘mobile’) – By default, SPR will use the mobile attribute to store mobile number enrollments when SMS is used. However, you may want to use another AD attribute to store this enrollment, for example in scenarios where you are allowing users to use their personal devices that you don’t want listed in the corporate directory, or if you are configuring the SMS service to instead use a third-party email address instead of a mobile number. This setting tells the Authentication Client what setting to check to see if the user is enrolled. This setting must be used in conjunction with a server-side setting that tells the service account which attribute to write the enrollment data.
Show tip about reset password link if the user account has been locked out – If the user enters a wrong password at the ctrl-alt-del/lock screen, and locks out their account, this setting will display a message to the user reminding them that they can use the “reset password…” link to unlock their account.
Show tip about reset password link when the user enter the wrong password – Same as above, but after each wrong password attempt, the client will remind the user that they can reset their password by using the link.
URL Overrides (SPR)
As I mentioned above, the client will use the URL’s found in the servers SCP. However, this is usually not the desired behavior as these URL’s will use the internal FQDN of the server. Most organizations want to use an alias instead e.g. pwreset.mycompany.com, as it is simpler, more secure ,and they probably already have a wildcard certificate that they can use.
This is also the case when you publish the service externally – you do not want to be using a real server name in your public DNS! To solve this particular issue you can simply add the custom URLs that you want to use, usually all of them, don’t forget you will need to add /specopspassword/reset, etc. after each FQDN.
https://pwreset.company.com/specopspassword/reset
https://pwreset.company.com/specopspassword/enrollment
https://pwreset.company.com/specopspassword/changepassword
https://pwreset.company.com/specopspassword/helpdesk
https://pwreset.company.com/specopspassword/reporting
I don’t want to use the ADMX files, I want to configure the registry instead!
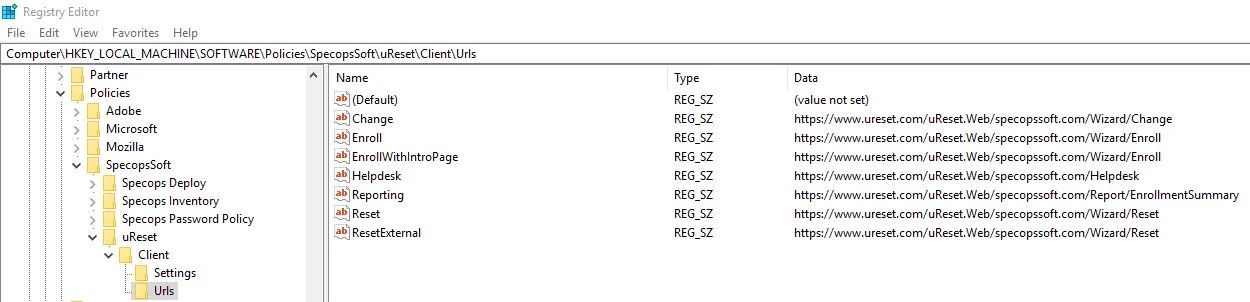
Some of our customers, for various reasons, do not want to use the ADMX templates. An alternative would be to use group policy preferences to write the GPO settings directly to the registry. If you take a look under Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\SpecopsSoft\uResetSpecopsSoft\uReset
This is where the settings are written. I suggest configuring a GPO to create the settings on a test machine and making a note of what is written to this key before defining your Group Policy Preference.
PLEASE NOTE! This is not a supported method as we may make changes to these settings, without notice, between releases.
That’s all the settings for Specops Password Reset covered, see the other (upcoming) blog posts for the other ADMX settings that affect the client for our other solutions.
Last updated on September 29, 2025