This website uses cookies to ensure you get the best experience on our website. Learn more
Active Directory reversible encryption explained
Table of Contents
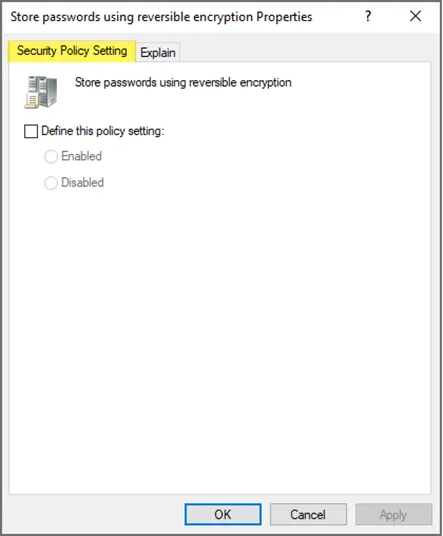
If you have administered password policies in Active Directory or looked at the local policies present in the Windows client operating system, you may have noticed an interesting setting contained in the Account policies section. The setting is Store passwords using reversible encryption. What is this setting, and why would you use it?
What is the ‘store passwords using reversible encryption’ setting?
‘Store passwords using reversible encryption’ is a policy setting within Active Directory that determines whether passwords are stored in a way that uses reversible encryption. It stores the passwords using a reversible encryption scheme that can be provided during the authentication process. Active Directory supports legacy applications that needed passwords in the clear-text form to function.
This policy is required when using some third party apps, but most commonly required with Challenge-Handshake Authentication Protocol (CHAP) authentication through remote access or Internet Authentication Services (IAS). It is also required when using Digest Authentication in Internet Information Services (IIS).
Why would you enable Active Directory reversible encryption?
The policy setting can apply to applications that use protocols that require knowledge of the user’s password in cleartext. By default, the user’s password history is non-reversibly encrypted, although, there are a couple of use cases that may require reversible encryption. To support some applications and their authentication, Microsoft permits the ability to store passwords using reversible encryption due to their required knowledge of the user passwords.
There are a couple of use cases where this setting would be enabled in Active Directory, for example:
- Challenge Handshake Authentication Protocol (CHAP) for remote access or Internet Authentication Services (IAS)
- Internet Information Services (IIS) Digest Authentication
- Running Specops Password Policy on Active Directory
With the above use cases mentioned, organizations will want to treat this setting with tremendous care as there are significant security implications from its enablement.
It is strongly recommended that organizations only enable reversible encryption if they are confident their Domain Controllers are secure.
Considerations when enabling and disabling reversible encryption
If your organization must enable this setting in Active Directory, there are a few guidelines to follow. These include:
- Make sure enabling the setting is necessary for your business.
- Use group policy to apply the setting to specific users granularly and not at the domain level for everyone.
- Keep in mind that if you enable the setting and then disable it, only new passwords will be stored using one-way encryption by default. Existing passwords will be stored using reversible encryption until they are changed.
Increasing the strength of Active Directory passwords
Organizations need to ensure that they have strong password policies in place for Active Directory. Aside from following best practice recommendations, there are other factors that can bolster password hygiene in the environment. These include checking the environment for breached passwords and proactive monitoring for these types of passwords.
Specops Password Policy and the Breached Password Protection service provide organizations with the automation needed to strengthen their password security posture. The solution blocks the use of a growing list of more than 4 unique known compromised passwords, found in data leaks, malware botnets, and live attacks via the Specops honeypot system.
Learn more about Specops Password Policy and download a free trial version.
(Last updated on March 25, 2025)