This website uses cookies to ensure you get the best experience on our website. Learn more
Ransomware attacks continue to rage on government entities
Table of Contents
Ransomware attacks are on the rise and target businesses across many industries and sectors. Government entities are also on the radar of ransomware gangs and have been the subject of many high-profile ransomware attacks. Governmental entities have been a high-level target for ransomware gangs for several reasons. Let’s look at ransomware attacks on governmental entities and note contributing factors leading to recent attacks. These include compromised passwords, breached passwords, and other types of password attacks.
What is a ransomware attack?
Ransomware attacks are one of the most devastating types of attacks that organizations can experience. Ransomware is a special type of malicious application that uses public key authentication to encrypt your data. The data is “locked” by the attacker in an unauthorized way until businesses pay a “ransom” to decrypt the data. This type of cyberattack is on the increase. One study indicated that ransomware incidents are up 600% from 2018 to over $20 billion in 2021. Attackers are also using more effective ways to force businesses to pay the ransom price demanded. For example, when organizations became smarter about having more robust backup solutions to recover data quickly, ransomware gangs implemented what is referred to as “double extortion.”
With the double extortion attack, attackers now demand additional ransom amounts to prevent the intentional leaking of critical or sensitive business data to the dark web. Arguably, data leakage can be the more devastating outcome of the two types of attack since the fallout from sensitive data leakage can last for years. In addition, some businesses never recover due to compliance violations, fines, and other consequences, such as lost consumer confidence.
Ransomware attacks on governmental entities
As mentioned earlier, commercial businesses are not the only targets of high-profile ransomware attacks. Governmental entities, such as city governments, have been the target of many attacks. Unfortunately, many city governments have been ill-equipped to deal with these attacks, making the damage and fallout even more severe.
Note the following recent ransomware attacks targeting city governmental entities, the results, and events leading up to compromise:
- Atlanta SamSam ransomware attack
- Farmington, New Mexico
- Colorado Department of Transportation
- St. Lucie Florida
- Riviera Beach
1. Atlanta SamSam ransomware attack
In March 2018, attackers launched a ransomware attack on Atlanta, Georgia’s computer networks and resources. The ransomware used was the notorious SamSam ransomware. The attackers demanded $51,000 in Bitcoin to unlock the encrypted resources. The city claims the ransom was not paid. However, the event ended up costing taxpayers an estimated $17 million.
SamSam typically utilizes brute-force attacks against weak passwords used on servers and other critical resources. RDP servers exposed to the Internet can be an easy entry point to launch a ransomware attack.
2. Farmington, New Mexico
The City of Farmington, New Mexico, suffered at the hands of SamSam ransomware and was demanded by attackers to pay $35,000 in Bitcoin to regain access to critical computer systems. The FBI recommended to city leaders not to pay the ransom demanded. Again, with SamSam ransomware, weak passwords are commonly involved with the compromise of exposed forward-facing resources.
3. Colorado Department of Transportation
Early on February 21, 2018, ransomware began spreading quickly in the Colorado Department of Transportation computer network. Due to a temporary, unsecured server placed temporarily on the Internet for testing, hackers were able to brute force the server and quickly gain access to the CDOT network. Ultimately, the ransomware attack cost the Colorado Department of Transportation $1.7 million in overtime, meals, and equipment.
4. St. Lucie Florida
In December 2019, a ransomware attack was launched via a phishing email that most likely came through an employee’s email. Hackers tried to extort $1 million from the St Lucie County Sherriff’s office using the DopplePaymer ransomware variant.
5. Riviera Beach
A ransomware attack hit the town of Riviera Beach, Florida, in June 2019, causing widespread disruption to the police department, fire department, and administration offices. The city had cyber insurance, which paid most of the $600,000 demanded by the ransomware group. After the attack, the city also invested some $900,000 in new hardware to remediate vulnerabilities found in the old hardware the municipality was using before the attack.
It was not disclosed which ransomware variant was responsible for the damages caused to the city. However, it does appear the attack started with a malicious phishing email opened by an employee.
Quickly secure passwords in the environment following an attack
As noted, often, the attack vector with a ransomware attack is weak or otherwise breached/compromised passwords in the environment. Therefore, when triaging matters after a ransomware attack, one of the first actions should be resetting all passwords in the environment. It is the most effective way to ensure passwords are safe following a ransomware attack. It is good to assume all passwords are compromised and react accordingly.
Most organizations use Microsoft Active Directory Domain Services (AD DS) to house authentication and authorization services. Active Directory passwords are often targeted by attackers using brute force, breached password lists, and password spraying attacks.
Seamlessly handle password resets with Specops uReset
Specops provides a Self-service Password Reset (SSPR) solution called Specops uReset. It allows organizations to handle mass password reset operations following a ransomware attack seamlessly. Additionally, Specops uReset helps alleviate the tremendous burden on the IT helpdesk with a mass password reset operation so the helpdesk can be involved with other matters related to ransomware cleanup operations.
As noted in a case study following a ransomware attack on the municipality of Kalix in Sweden, Specops uReset was instrumental in allowing some 2000 passwords to be quickly reset using the self-service uReset portal.
Kenneth Björnfot, Head of IT for Kalix, explains the password reset operation using Specops uReset:
“We locked all accounts and informed our staff that they would need to authenticate with Mobile BankID to set a new password,” Kenneth says. “Everyone is familiar with BankID, so it was very easy for them to authenticate themselves and reset their passwords. And from IT’s point of view, we know that the process is secure.”
Using the Mobile BankID, stored in an Active Directory attribute, Kalix was able to rollout Specops uReset, allowing a seamless experience for Kalix employees.
“The staff went to the correct URL, authenticated themselves with Mobile BankID, and were instructed to set a new password. The new password requirements are more stringent to prevent the use of insecure passwords.”
Specops uReset provides the following features:
- Specops uReset is available from a web browser connection
- You can update the locally cached credentials for remote users
- Helpdesk professionals have an interface to verify the end-user password resets via the Secure Service Desk
- Organizations can perform enrollment enforcement and have auto-enrollment options
- Enrollment notifications can be notified via the system tray, email, or enforced using an unclosable fullscreen browser
- Admins get statistics and audit reporting
- Multi-language interface
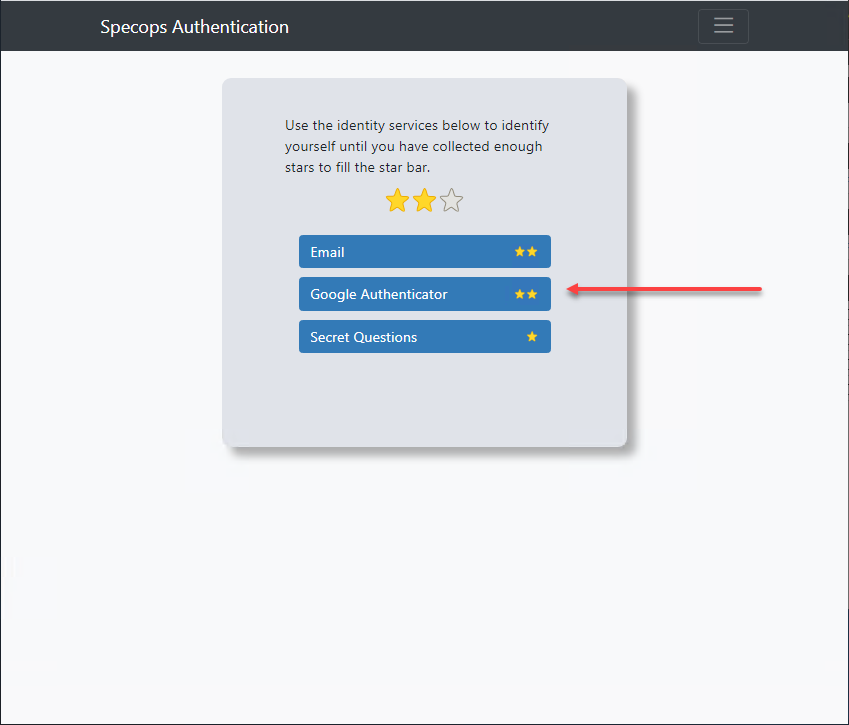
- You can verify user identity using 15+ identity providers for multi-factor authentication (MFA)
- Organizations can customize the user interface, changing the text, logo, and colors
- Enforcement of Google re-CAPTCHA to prevent username harvesting
Specops uReset helps organizations gracefully deal with the challenging prospect of mass password resets. It ensures businesses can quickly secure all passwords in the environment to meet strong password policies and offer this capability in a self-service password reset solution. Learn more about Specops uReset.
Ransomware attack FAQs
- What is a ransomware attack? Ransomware is a special type of malicious application that uses public key authentication to encrypt your data. The data is “locked” by the attacker in an unauthorized way until businesses pay a “ransom” to decrypt the data. This type of cyberattack is on the increase.
- What is double extortion? With the double extortion attack, attackers now demand additional ransom amounts to prevent the intentional leaking of critical or sensitive business data to the dark web
- Why reset passwords after a ransomware attack? Many times, attackers get compromise an environment with weak or breached passwords. Forcing a password reset on all accounts ensures any compromised passwords are remediated
(Last updated on November 5, 2024)


