This website uses cookies to ensure you get the best experience on our website. Learn more
What metrics should sysadmins use to show improvement over time?
Table of Contents
To illustrate how essential IT systems are to the proper functioning of the business, system administrators should use a number of metrics to communicate key KPIs with non-technical leadership. This can help justify the overall budget of the IT department, as well as the future growth of systems and resources.
Uptime of key systems
One of the best places to start is by looking at the uptime of all essential business systems. If employees are unable to do their job, or customers are unable to make a purchase, that is going to be a major problem. Another related metric is uptime improvement over time, which is often measured in mean time between failures
You should always be monitor network availability and use that data for future improvements and upgrades. Metrics such as 99.9% network availability may be too vague. Providing leadership teams with business-focused information may be more valuable. For example, reporting that there were zero network outages during business hours, and two outages lasting a total of 15 minutes outside of business hours is generally more helpful.
Reduced helpdesk tickets
One of the most frequent types of helpdesk tickets are related to account management. For example, end users might be locked out of a system, and require a password reset. Without a self-service password reset system in place, these types of calls can amount to almost half of all helpdesk tickets.
A self-service password reset solution, like Specops uReset, can track self-service password resets in Active Directory, that would have otherwise gone to the helpdesk.
Security improvements
In 2020, 80% of data breaches stemmed from stolen or brute-forced credentials. This means that passwords play a critical role in improving the overall IT security of a company. You should begin by examining how your existing password policies. Free tools such as Specops Password Auditor can help you scan Active Directory for password-related vulnerabilities. You can even generate reports to see exactly which accounts are using breached passwords.
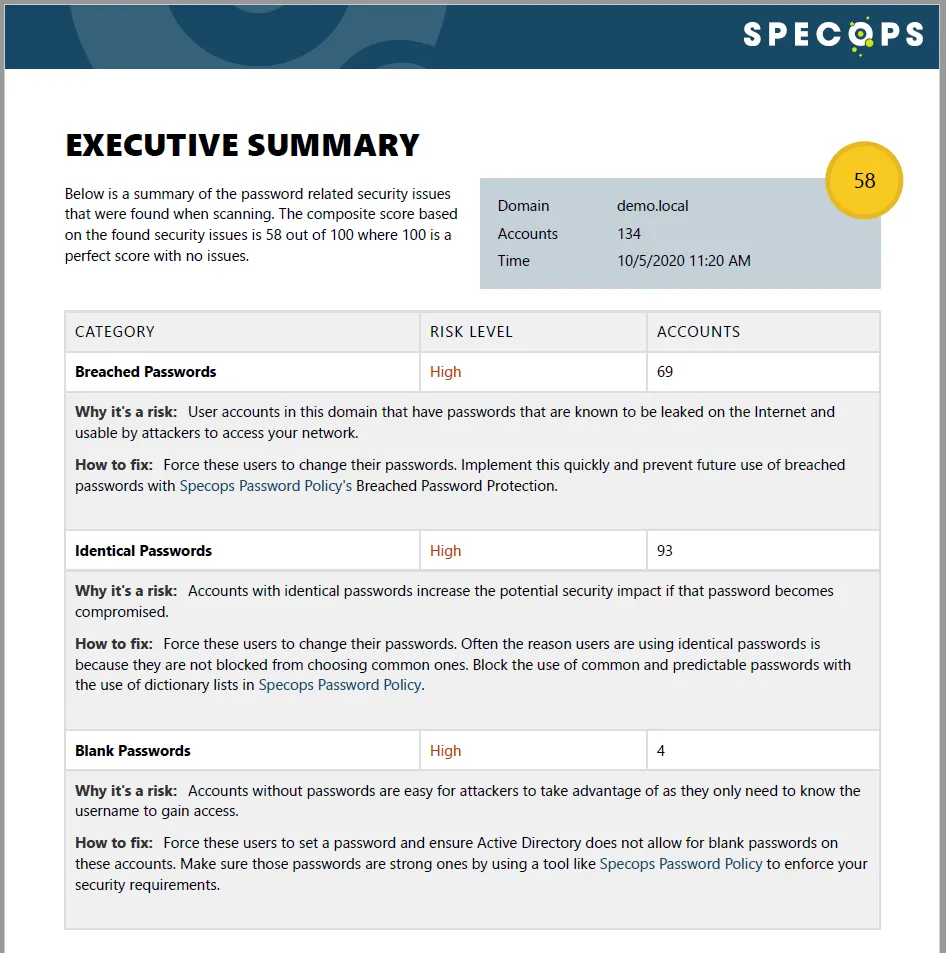
Once these accounts have changed their password, you can run the report again. As your score improves over time, you can use the metrics as security improvements.
Using the right metrics
At the end of the day, every sysadmin will want to use a unique set of metrics relevant to their systems. Taking the time to create the right reports will show the quality of individual performance, and the value of the IT infrastructure.
Last updated on March 31, 2025


