This website uses cookies to ensure you get the best experience on our website. Learn more
Hybrid password attacks: How they work and how to stop them
Table of Contents
Cybersecurity measures force threat actors to get creative and come up with new and inventive ways to compromise user credentials. As the name suggests, hybrid password attacks involve combining two or more attack methods to carry out password cracking. Taking advantage of the strengths of different techniques can greatly speed up password cracking – especially if an organization has allowed weak or compromised passwords to be used.
How do hybrid attacks work?
In a hybrid attack, threat actors integrate the methodology of two or more attacks. It’s this blending of techniques that makes hybrid attacks potent and dangerous. This isn’t just limited to password cracking – the term also broadly applies to threats that blend conventional cyber-attacks with other tactics. For example, a state-sponsored threat actor might combine malware attacks with disinformation campaigns on social media to destabilize a target nation. This mixing of various attack methods makes hybrid threats more complex to defend against.
When it comes to passwords, a typical hybrid attack involves combining dictionary and brute force techniques. The former contains a word list of commonly breached credentials, and the latter applies rapid iterations of character swaps and combinations to each. We’ll explore each in a bit more detail.
Dictionary attack
A dictionary attack is when attackers use a predefined list or ‘dictionary’ of likely possibilities to guess passwords or decryption keys. These could range from frequently used passwords and common phrases to regularly used terms in specific industries, or ‘keyboard walks’ such as ‘QWERTY’. This attack preys upon the human tendency to opt for simplicity and familiarity when creating passwords. Hackers can use social media platforms to gather intel about users, potential usernames, and what industries individuals may work in, giving insights into the types of passwords they may choose.
However, it’s often simpler than that. The Specops research team looked at passwords being used to attack RDP ports in live attacks and analyzed a subset of over 4.6 million passwords collected over the span of several weeks – we found that ‘password’ was the most common base term, followed by ‘admin’ and ‘welcome.’ Of course, many users will add at least a small amount of variation to these terms, which is where brute force techniques come in.
Brute force attack
Brute force attacks display a more persistent and blatant method of operation. In these attacks, the threat actor uses software to attempt all possible character combinations until the correct password or decryption key is found. While this method might seem labor-intensive and time-consuming, it can be highly effective against shorter or less complex passwords – especially when given a head start by using common base terms found in dictionary lists.
Using the example from above, ‘password’ could be the base term from a dictionary. The brute force attack will try all subsequent variations such as ‘Password, Password1, PASSWORD, PASSWORD2’ and so on. Blending these methods improves the attacker’s success rate by considering both the likelihood of users using common words and the typical variations people use in order to meet their organization’s complexity requirements.
Mask attack
A mask attack is a sort of brute forcing, where attackers know elements of a password construction and can therefore reduce the amount of guesses they’ll need to get it right. For example, an attacker might know a password is eight characters and the last one is a number. Or they might now a company has a poor policy such as adding the current month and year to the end of passwords when rotating them. Having any sort of definitive information about the makeup of a password can greatly speed up a hybrid attack.
Strategies to counter hybrid password attacks
Hybrid password attacks are effective because they combine to target the weak points in an organization’s password policy. The best defense is a comprehensive strategy to root out weak and compromised passwords, then creating a stronger password policy to maintain security going forward. Just as attackers layer their attack techniques, we need to layer our security defenses too.
Multi factor authentication (MFA)
Requiring users to authenticate themselves with something additional beyond their password can stop an attacker if a password is cracked. MFA is an important part of a password security strategy but remember it’s not a silver bullet. Attackers have work-arounds available – such as MFA prompt bombing.
Block weak passwords
Dictionary and mask attacks rely on easily-guessed or known words and patterns to greatly speed up brute force techniques. Blocking users from using universally weak words and patterns, as well as easily-guessed words unique to your organization, takes away an attacker’s advantage.
Enforce longer passwords
Brute forcing passwords becomes computationally impossible at certain lengths. Encouraging users to create passphrases comprised of three random words at around 20 characters can essentially nullify the threat of brute force attacks.
Check for compromised passwords
Even if your password policy blocks users from creating weak passwords, strong passwords can still become compromised via a phishing attack or other breach. You also can’t know if a user has reused their strong work password on personal sites or applications with weak security. It’s often hard to tell until it’s too late, so having a tool that can scan your Active Directory for compromised passwords is key.
Interested in learning how many of your users’ passwords are already compromised? Run a fast and free scan of your Active Directory with Specops Password Auditor against a list of over 1 billion unique compromised passwords.
How Specops can enhance your password policies
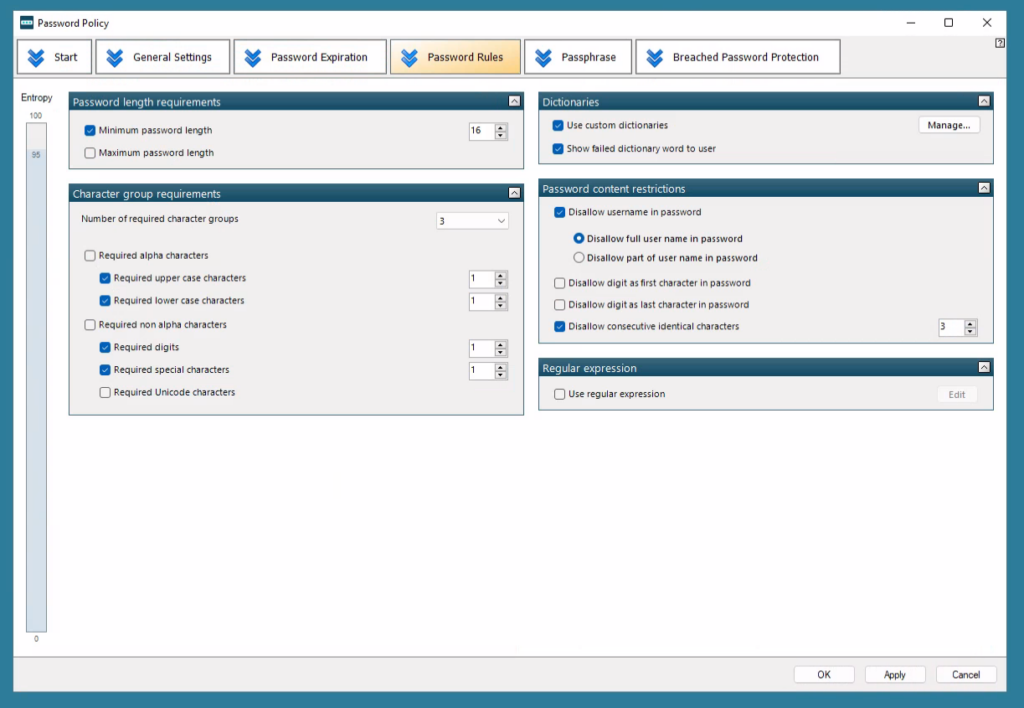
Addressing hybrid threats requires a comprehensive approach and password policies play a crucial role in defending against hybrid threats. Specops Password Policy enforces stringent and customizable password requirements, checks against known breached passwords, and guides users toward creating secure passphrases.
By helping users to create strong and complex passwords, Specops significantly reduces the likelihood of hybrid attacks. This efficient and practical approach to password security empowers organizations to protect their essential data and maintain the integrity of their systems. In addition, as organizations are increasingly transitioning to SSO solutions sourced from on-premises Active Directory solutions, Specops helps ensure their Active Directory password security is as secure as possible.
In the face of escalating hybrid threats, increasing password security isn’t just an option—it’s an absolute necessity. Sign up for a free trial of Specops Password Policy today: Specops Password Policy.
Hybrid Password Attacks FAQ’s
Hybrid password attacks blend one or more attack techniques to crack users’ passwords. The most common combination is a dictionary and brute force attack. If some of the password structure is known, mask attacks can also be used.
Countering hybrid threats requires a comprehensive password policy that enforces multi-factor authentication, blocks weak words and patterns, scans for compromised passwords, and encourages users to create lengthy passphrases.
Specops Password Policy can play a vital role in strengthening your cybersecurity defenses. It helps organizations enforce strong password policies, prevent data breaches, and secure user authentication, which are crucial in the fight against hybrid attacks.
(Last updated on May 14, 2025)