This website uses cookies to ensure you get the best experience on our website. Learn more
How to configure the initial password for remote onboarding of new employees
Table of Contents
Many organizations now have a large remote workforce. Servicing this user base has a certain set of logistical and security challenges. One of these challenges includes securely setting and delivering an initial password for remote onboarding of new hires. Often, this is the first step in configuring MFA.
With the release of Specops First Day Password (FDP), organizations with Specops uReset can securely deliver an initial password experience secured by another factor. The solutions allows new users to set their password and sign into their Active Directory account – without using a previously assigned password that is shared insecurely, or verbally.
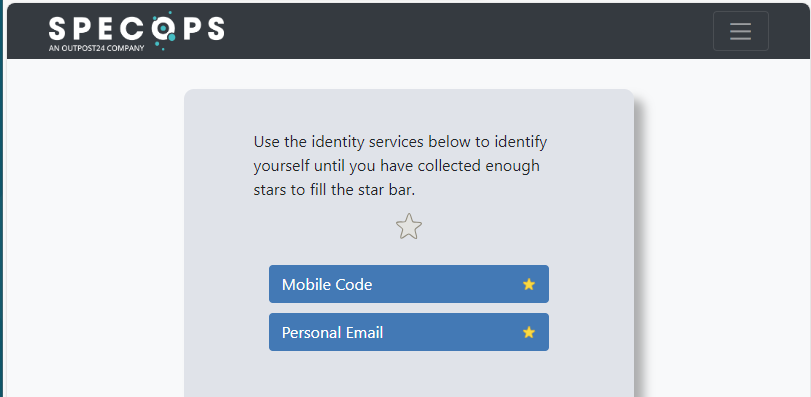
Currently FDP supports Mobile Code and Personal Email as initial user verification factors. These are both things typically captured by HR during onboarding. These factors can then be securely used in uReset (without visibly publishing them in Active Directory) via the Specops Authentication sub-object under the user’s own AD object.
The following scenarios are supported by the solution:
- IT deploys the desired OS and apps and pre-creates the user’s profile before shipping so the user can do Reset Password before logging in. This would require the user to be pre-created in AD and then have their account configured for FDP.
- IT deploys the PC, and the organization uses an always-on VPN based on device authentication. The user can then sign in with no staged profile using Reset Password powered by FDP.
- The user securely creates their new password using Specops First Day Password on their own personal device. The user would sign in to their new PC shipped directly to the remote user from the manufacturer or IT. This would leverage Microsoft Autopilot/Intune or another MDM to deploy the needed software AFTER the user navigates the OOBE interface.
This allows the user to securely set the AD password and then perform any other enrollment required by corporate policy.
How to test your FDP workflow
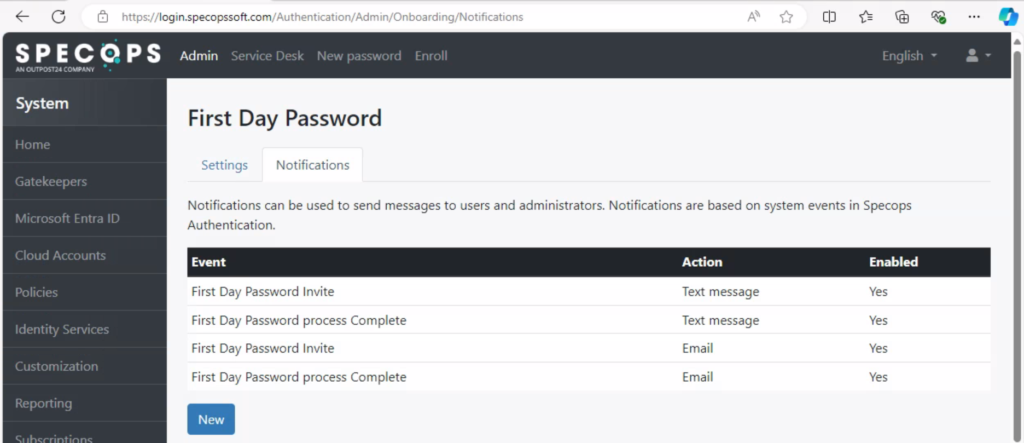
Once the feature is enabled in the uReset subscription, the initial settings and notifications should be configured in the Specops Authentication admin portal.
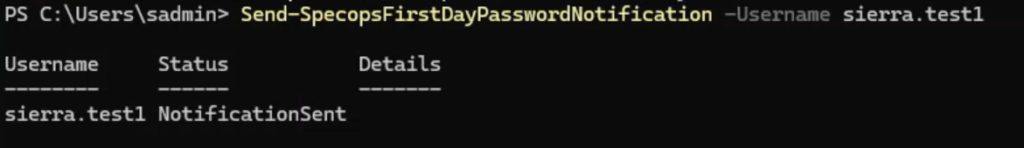
Then, the user process starts by identifying the user object that needs to be sent an FDP workflow and their individual information. Now, open PowerShell where the Gatekeeper Admin tools are installed. If you need to enroll many users or bulk import, see this post.
Run Get-SpecopsFirstDayPassword to see if there are any pending onboarding objects for FDP. If no users are pending, the output will be null.
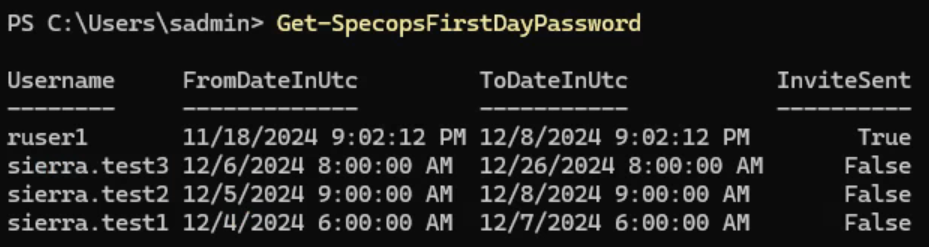
Now we can Set-SpecopsFirstDayPassword and provide the required factors. A username and either a mobile number or personal email must be specified. Start date and days that First Day Password will be available are also optionally configurable.
Set-SpecopsFirstDayPassword -Username sierra.test1 -PersonalEmail specops.test1@gmail.com
-UserMobile +12155550123 -FromDate "12/04/2024 06:00" -ValidNumberOfDays 3Once the user has been set for onboarding the next step is to enable onboarding reminder delivery upon next scheduled user counting in the admin web.
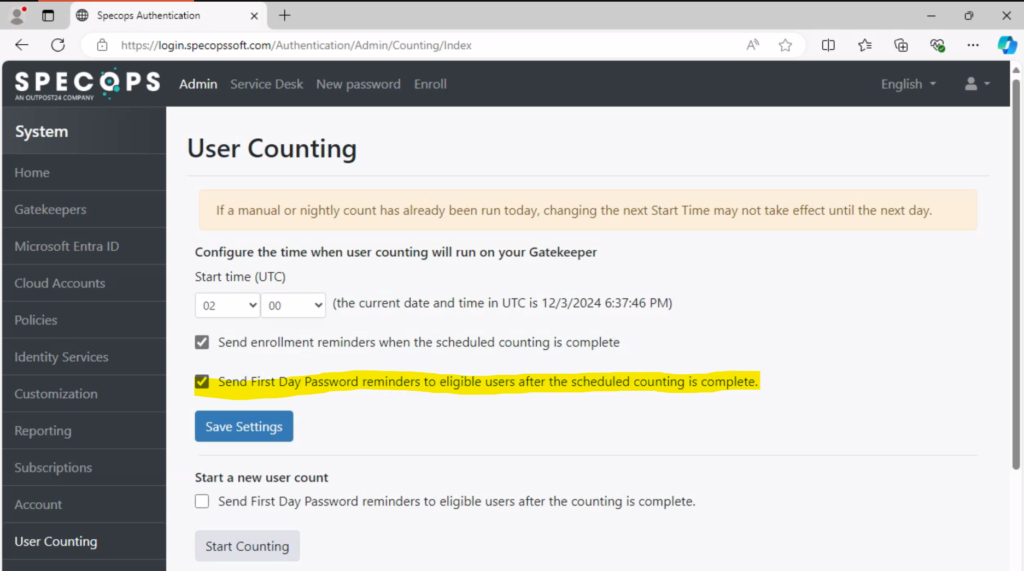
Once the nightly user counting is complete, the onboarding invites will be delivered based on the configured notifications. The invites can also be sent out manually by using the Send-SpecopsFirstDayPasswordNotification cmdlet.
The initial password experience for new hires
The user will receive the following email:
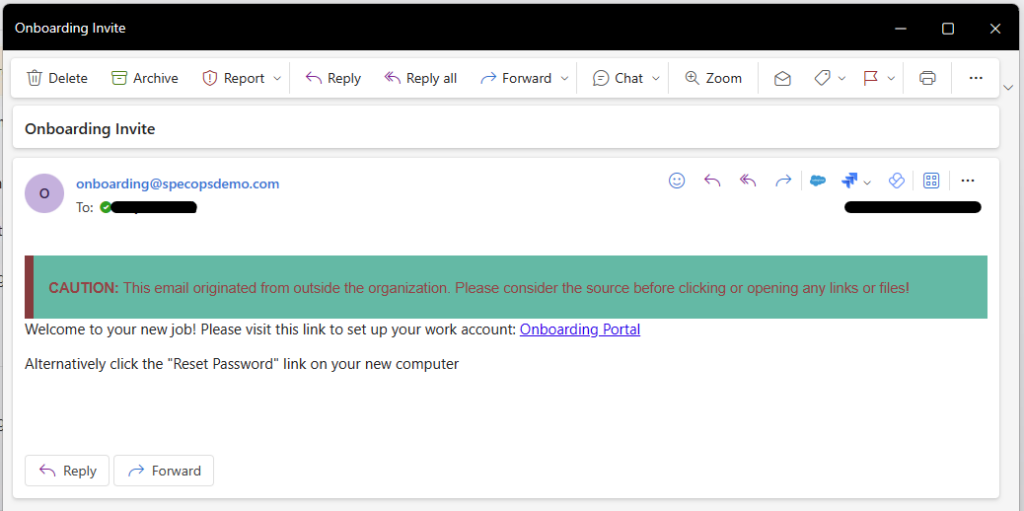
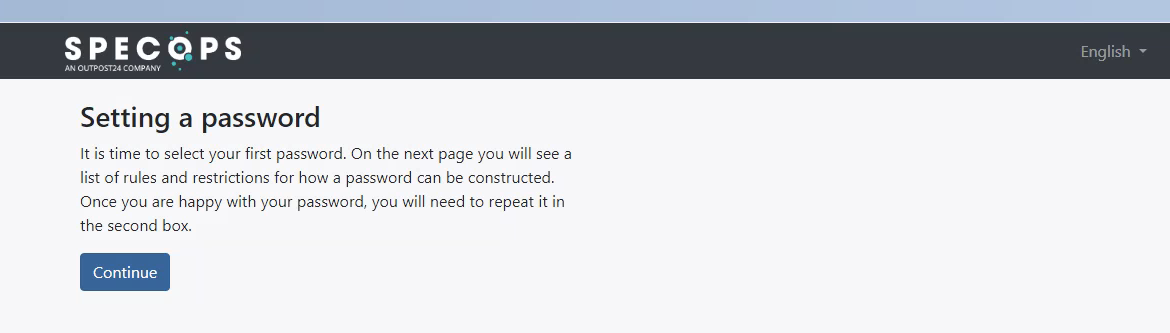
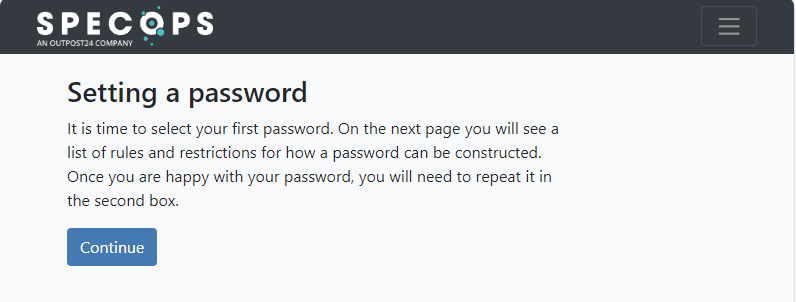
After they click on the Onboarding Portal link, they will be taken to the following page to set a password.
They will then be asked to verify their identity via the configured identity services:
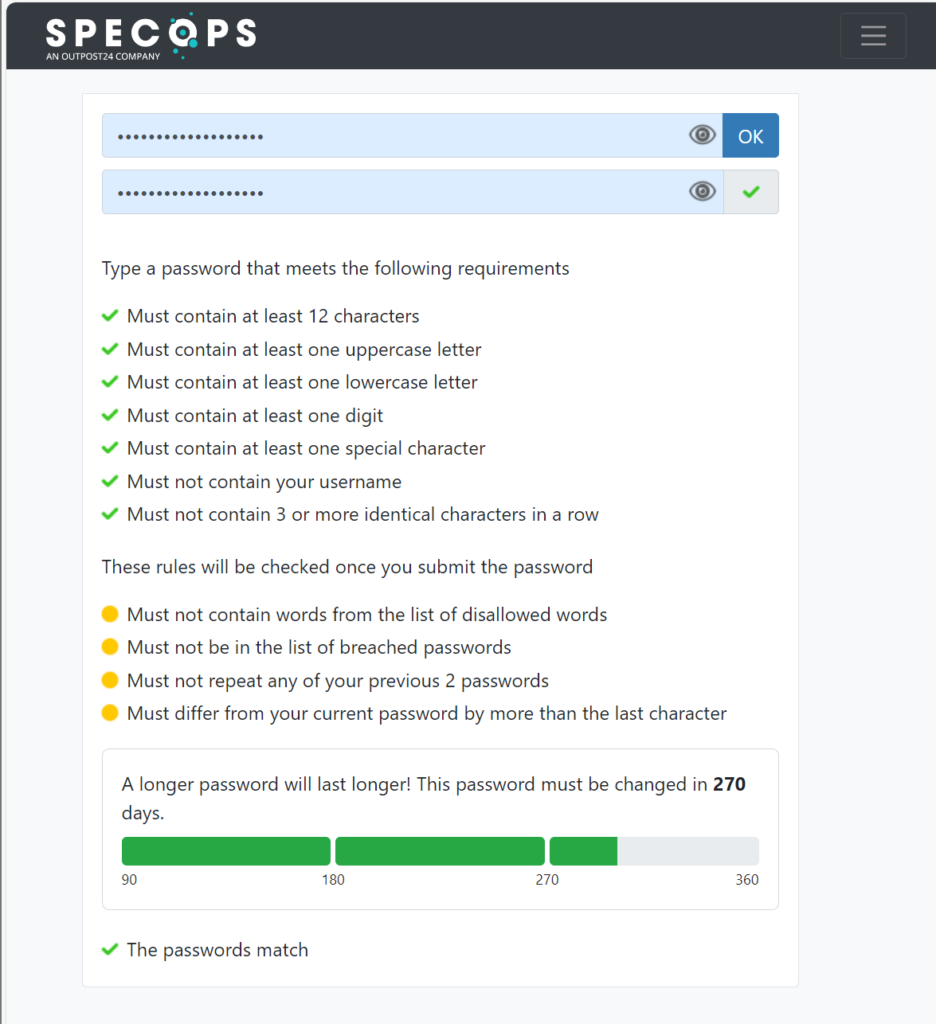
The password creation page. If Specops Password Policy is configured, they will receive helpful feedback to set a secure password aligned with the password policy.
If the password meets the policy requirements, the user will receive the following message.
Now the user has satisfied the requirements for FDP and can use their AD account.
Last updated on May 9, 2025


