This website uses cookies to ensure you get the best experience on our website. Learn more
Active Directory honeypot accounts: How to keep attackers sweet
Table of Contents
Monitoring and detecting account compromise is one of the most challenging tasks for IT admins and SecOps professionals. Once a legitimate account has been compromised, it can be difficult to detect an attacker’s activities until it’s too late and damage has already been done. And if a privileged account is compromised, an organization can be in serious trouble.
We’ll run through how Active Directory honeypot accounts can allow you to spot unusual account activities once they’re already underway in your environment, and how to collect valuable threat intelligence to shape your future security defenses.
How honeypots work to lure attackers
A honeypot is a computer or network system that looks real but is a decoy to lure in attackers and gain information about how they operate. Honeypots can also serve as a distraction to lure attackers away from actual production systems.
Unlike other defensive mechanisms, a honeypot’s sole purpose is to gather information. Organizations can use the information collected from a honeypot to feed into their cybersecurity defenses and block known attack IP addresses, specific network traffic, geolocations, and even vulnerable passwords.
Active Directory honeypot accounts
An Active Directory honeypot account can be made to look like a highly desirable account for attackers to target, such as a high-level admin account with far-reaching access to various systems and applications. Mimicking a real privileged account, while limiting what the account can actually do, is the technical challenge with honeypot accounts. But with careful preparation, it is possible.
When an attacker is carrying out reconnaissance of an organization’s Active Directory, they will be looking out for a few key things. They will be keeping an eye out for privileged accounts with old passwords, regular use, and associated Kerberos Service Principal Names (SPNs).
So, let us consider a few red flags that may tip off an attacker that the account could be a honeypot account, and not an actual account they are attempting to compromise. This can help IT Security teams understand how honeypot accounts need to be configured and placed in the environment to have the appearance of legitimacy.
How an attacker might detect a honeypot account
Honeypots are no secret. When defining and using Active Directory honeypot accounts, it is important to remember that attackers will proceed cautiously and look for the telltale characteristics that an account may be deliberately there as bait.
If an attacker has compromised the environment, and starts reconnaissance on user accounts, they will look at the following user characteristics:
- When was the account created? If the account were created recently or in the last several months, attackers may assume this account could potentially be a honeypot account and steer clear, especially if the login date is roughly the same as the creation date.
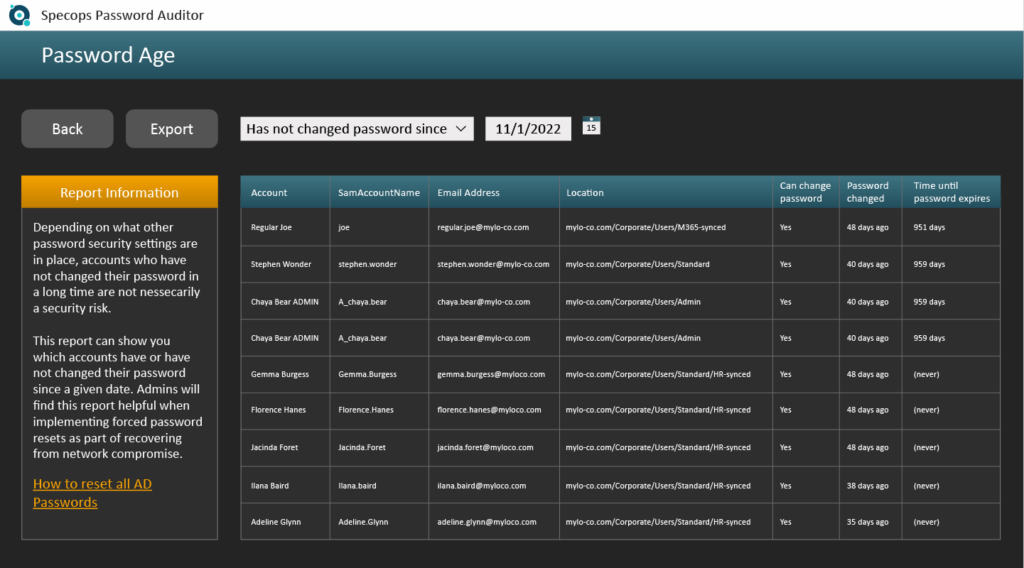
- When was the password last set? If the password has not been set since the account was created, attackers may view this as a honeypot account.
- Have there been any bad password attempts recently? If the account has no bad password attempts, it may appear suspicious since a real, active account will most likely have a bad password attempt at some point.
- Is there an associated Kerberos SPN? If so, attackers can look at various characteristics of the SPN to determine if it is a real SPN used in the environment. If not, they might suspect it is not a legitimate account.
Five tips for creating an Active Directory honeypot account
With the above factors in mind, here are some tips for creating accounts that should look legitimate in the eyes of an attacker:
- Use an old account you can recycle for the honeypot account. However, make sure it’s associated with a user and has had some use down the years, as a totally inactive account not linked to a user will look suspicious to an attacker.
- Automate a way to log in as the user with a script or some other means to give it the appearance of an account used in the environment. This should help trick the attacker into thinking it’s a regularly used account, even if there were some periods of inactivity in its history.
- Use an old password, but one that has been reset a few times. It will look suspect if this account has had the same password for 10+ years while other privileged accounts have been forced to reset theirs. You should also make sure there are some bad password attempts in there for added realism.
- If you decide to add the honeypot account to a privileged group, make sure it looks like the other privileged accounts and does not stand out in any obvious way. Also, proceed with caution. If added to a privileged group, place limitations on the account – such as devices and applications it can log into, or time of day restrictions to help control the scope of what the user can do.
- Heavily monitor the account. The whole point is to track what attackers are doing and gain valuable threat intelligence. Without close monitoring, a honeypot account is pointless.
Collecting data from Active Directory honeypot accounts
Honeypots provide valuable data that IT Security teams can use to design appropriate security measures against real threats. For example, knowing the password used against a honeypot account can be extremely useful for configuring the Active Directory password policy, or blocking vulnerable passwords altogether.
Specops Software maintains a global honeypot system (one of our sources for compromised passwords blocked by Specops Password Policy and Breached Password Protection) which collects passwords used in real attacks on the system’s endpoints. This data can be extremely valuable for IT admins who want to block these vulnerable passwords from being used in their Active Directory.
Access to all the data from our system of global honeypot accounts can be yours. To decrease the chance of a malicious login attempt on your organization’s Active Directory accounts, book a free trial of Specops Password Policy.
Last updated on November 11, 2025





